Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
InfoSec Book Excerpt: Security Metrics - Chapter 17

Soft Skills: A Peek into the Mind of a Hiring Manager

How to Build a Secure RPC Interface for AJAX Apps With Google Web Toolkit

Circumventing NAT with UDP hole punching

CSRF and XSS: A Lethal Combination - Part I

Information Gathering Using Maltego

pcAnywhere Leaked Source Code - An Anonymous Review
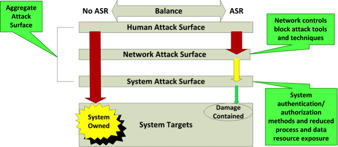
Attack Surface Reduction – Chapter 4

Virtualization Security: Hacking VMware with VASTO
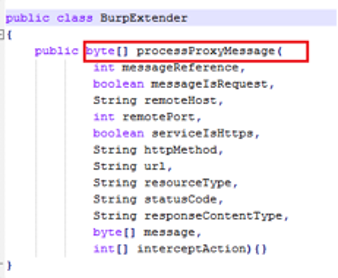
Extending Burp Suite

A New DNS Exploitation Technique: Ghost Domain Names

RootSmart Android Malware

Attacking the Phishers: An Autopsy on Compromised Phishing Websites

Creating backdoors using SQL injection

Top 10 Tips for Securely Managing Your Employee’s BYOD
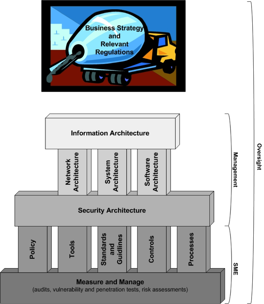
Building the Foundation: Architecture Design - Chapter 3

Writing Self-Modifying Code Part 3: Antivirus Evasion

Hacking In The World’s Largest Mall

Wi-Fi Security: The Rise and Fall of WPS

Burp suite walkthrough

Under the Hood: Reversing Android Applications

A Few Words on Malware - The Sality Way

Hacking web authentication - Part 2

Inserting Vulnerabilities in Web Applications