Infosec Skills release: New Bash scripting, threat hunting and auditing courses
June 06, 2020
Three new learning paths are live in Infosec Skills: Offensive Bash Scripting, Cyber Threat Hunting and Cybersecurity Audit Fundamentals. Your Infosec Skills subscription now includes unlimited access to more than 800 courses, browser-based labs, hands-on projects and other training content.
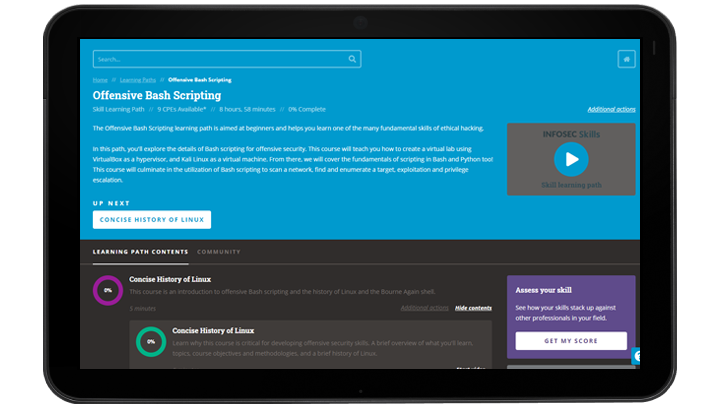
Offensive Bash Scripting Learning Path
Learn one of the fundamental skills of ethical hacking in the Offensive Bash Scripting Learning Path. You’ll start by creating a virtual lab using VirtualBox and Kali Linux. Then you’ll explore foundational concepts, such as:
- File permissions and processes
- Network reconnaissance
- Traffic analysis
- Enumeration
- Process automation
- Network monitoring
- Testing for common app vulnerabilities
- Privilege escalation
The path culminates in an Offensive Bash Scripting Project where you’ll put your new skills to the test by hacking a virtual machine named Kioptrix 2.
Cyber Threat Hunting Learning Path
Learn what it takes to become a cyber threat hunter in this new Infosec Skills learning path. You’ll explore a variety of common cyber threat hunting tools and techniques as you master a repeatable, documentable cyber threat hunting methodology, including:
- Intelligence gathering
- Detecting anomalies in network traffic patterns
- Investigating malicious activity
- Responding to cyber threats
- Remediating malware
In the Cyber Threat Hunting Project, you’ll investigate a potential malware infection using your new skills. Can you piece together the clues and hunt down the threat?
Cybersecurity Audit Fundamentals Learning Path
Explore best practices and controls used to reduce an organization’s risk in the Cybersecurity Audit Fundamentals Learning Path. Some of the topics covered include:
- Audit’s role in reviewing cybersecurity controls
- Why governance is critical to cybersecurity
- Different components of cybersecurity operations
- Different types of digital assets and the controls to protect them
By the end of the path, you’ll know how to identify effective, efficient and reliable controls that satisfy compliance requirements and maintain confidentiality, integrity and availability.
For more information on upcoming features and content, see our Infosec Flex and Skills product roadmap and our LX Labs content roadmap.