Learning x86 disassembly gives you the "keys to the kingdom," says Infosec Skills author Stephanie Domas
Assembly language is often overlooked as an important skill for cybersecurity professionals, but Infosec Skills author and cybersecurity expert Stephanie Domas is turning that concept on its head. She’s shouting from the rooftops about the high value of learning x86 disassembly.
“My passion is to teach people, and it’s actually the most powerful piece of cybersecurity,” Stephanie said. “A lot of people want to focus on a system’s higher levels because it’s flashier. But if you can control a system at its most fundamental level, you've got the keys to the kingdom. The truth is it's learning how a computer actually works.”

Learn Python for Cybersecurity
Understanding machine code and assembly language
Assembly language is the human-readable version of machine code — what a computer’s processor is actually running every time you move your mouse and click. Machine code instructions are a series of ones and zeros and nearly impossible for a human to read. Assembly is one step up from that.
For cybersecurity professionals, learning assembly benefits both reverse engineering and forward engineering perspectives. From an offensive security perspective, it can be used to help proactively identify weaknesses and break systems. From a defensive security perspective, knowledge of assembly can help lock down software.
Learn x86 disassembly with hands-on training
Stephanie's learning path, Introduction to x86 Disassembly, teaches you how computer processors truly execute code. You’ll learn how to read and write your own code, and how to build your own pure assembly applications. Upon completion, you’ll have the knowledge to write, compile and debug pure assembly applications or start to debug and dissect other people’s applications.
The learning path includes six courses covering everything from the basics to debugging and logic flows. Developers, security engineers, reverse engineers and anyone wanting to add x86 disassembly to their skill set will benefit.
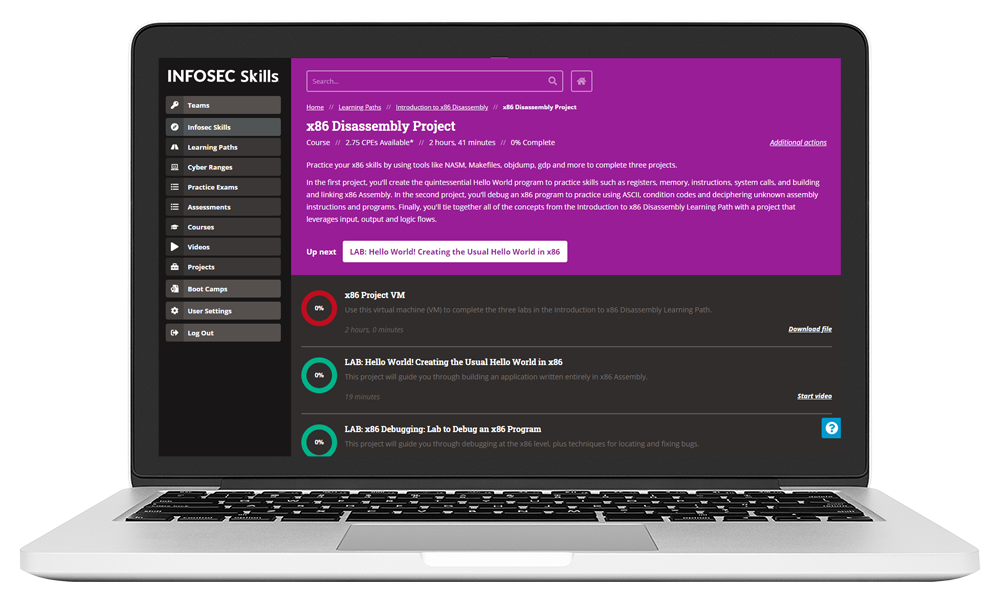
The learning path also includes a hands-on x86 Disassembly Project. Stephanie is a strong believer in learning by doing so she built the three-part project as a way to practice your newly learned x86 skills. You’ll use tools like NASM, Makefiles, objdump, gdp and more to complete the projects:
- In the first project, you'll create the quintessential Hello World program to practice skills such as registers, memory, instructions and system calls.
- In the second project, you'll debug an x86 program to practice using ASCII and condition codes, as well as decipher unknown assembly instructions and programs.
- Finally, you'll tie together all of the concepts with a project that leverages input, output and logic flows.
Advance your career and earn more money
When not authoring Infosec Skills learning paths, Stephanie is an executive vice president at MedSec, a research and security provider for healthcare manufacturers and vendors. She also regularly teaches, mentors and speaks at conferences where she evangelizes on the power of x86 disassembly.
“We have this huge talent gap in the cybersecurity workforce,” she said. “This knowledge can help fix that problem while also boosting your employability. It's such a valuable skill set from a monetary standpoint. If you're an X86 security expert you're going to have job offers thrown at you. So x86 has become a crusade of mine."
“It’s smart for defensive cybersecurity people to learn how the offensive cybersecurity people crack software," Stephanie said. “If you can understand assembly at that level and understand the offensive techniques being used, it will make you way better at defending those systems. Companies can’t recoup the investment of millions of dollars in R&D because somebody cracks it, somebody puts a key generator for it online, somebody figures out how to cheat at the game and bypass in-game currency. There's a lot of value for the defensive side if they understand assembly and how these systems are attacked.”

Intro to x86 Disassembly
About Stephanie Domas
Stephanie Domas is Executive Vice President at MedSec. In this role, she leads the development of cybersecurity products and services to support medical device manufacturers on design, architecture, security risk management, regulatory filings, penetration testing and execution of security best practices in the development of medical devices, as well as vulnerability and asset management of connected medical devices in hospitals.
Mrs. Domas has spent 10+ years doing security research at the x86 level. She is emphatic that whether your goal is to be a better developer, security researcher, or reverse engineer, knowledge of assembly is crucial. She is passionate about spreading the joy of x86 and routinely teaches training and speaks on x86 assembly at security events such as Blackhat, Defcon and Derbycon.








