52 NICE Cybersecurity Workforce Framework work roles: What you need to know
Introduction
In the US, Chinese restaurant menus usually have many combination plates available for lunch or dinner, each representing a particular grouping of ingredients in a specific ratio. These combinations can grow to huge numbers, sometimes into the hundreds at particularly busy restaurants.
Having common reference points for these particular combinations, sometimes only with very small differences, can make massive dividends when trying to reduce the amount of time required to produce a product. It also makes sure that people potentially speaking different languages have a common point of reference.

Learn Windows 10 Host Security
Being able to have a list of exactly what you're looking for in these types of scenarios can make things far easier for whoever is doing the ordering, even if it does take some research as to what each number means. This principle can be applied to more than just food orders though, as in the case of the 52 work roles that are listed as part of the National Initiative for Cybersecurity Education (NICE) Cybersecurity Workforce Framework. Like on our menu analogy, there are many different combinations to choose from, with each one dialed in to particular skill sets and having specific values — this allows for multiple departments to speak their own languages when it comes to who they are looking for.
One critical thing to remember about the NICE Framework is that it is a National Institute of Standards and Technology (NIST) Special Publication. What this means is that in addition to being a set of guidelines and recommendations for the industry as a whole, it may be a binding required set of rules that MUST be followed for some specific applications such as government work. You may need to do some additional research if this applies to your sector.
Breaking down the seven categories
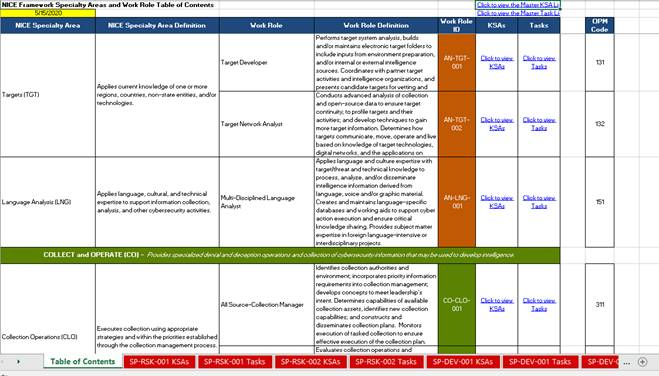
If you've ever looked at a typical set of requirements for cybersecurity certifications or other types of class-based requirements, you may already be aware of the concept of domains or categories — general buckets that specific groups of ideas fall into. In the case of the NICE Framework, there are seven broad ideas that contain top level concepts as shown in the table below:
From these seven categories come 33 specialty areas, which then break off into the individual work roles to make 52 total roles.
How to use the NICE Cybersecurity Workforce Framework
In order to use the Framework, NICE publishes two key documents, available here.
The first is a PDF document which lists and codifies the framework itself and each of the Knowledge, Skills and Abilities (KSAs) and Tasks associated with each work role. However, due to the sheer size of this document, the supplied Excel spreadsheet is recommended for daily use. This helps to manage a lot of the massive amount of information being thrown at you.
The table of contents breaks down each Category, Specialty Area and Work Role into manageable chunks. For example, in the screenshot above, you can see the Category “COLLECT and OPERATE” with the Specialty Area “Collection Operations” listed below it, along with associated Work Roles and links to KSAs and Tasks.
The color for each Work Role ID references the Category it belongs to. So for example, the All Source — Collection Manager shows as green for Collect and Operate, while the brown Work Role IDs belong to Analyze. This helps to show you at a glance what section you are in so you don't get lost in, what is by necessity an incredibly large document.
Each Work Role has two associated worksheets: its KSAs and Tasks. KSAs and Tasks both come from a master list which are commonly used across all Work Roles. The Excel spreadsheet is very useful for finding out what is associated with particular Work Roles; however, this sometimes isn’t quite what’s required for your situation. If you need to work backwards from what is associated with a particular piece of knowledge, the Department of Homeland Security (DHS), which helped to co-author the NICE Framework, has created a portal which can help search across the framework by almost any reference point. This portal can be accessed here.
Example usage
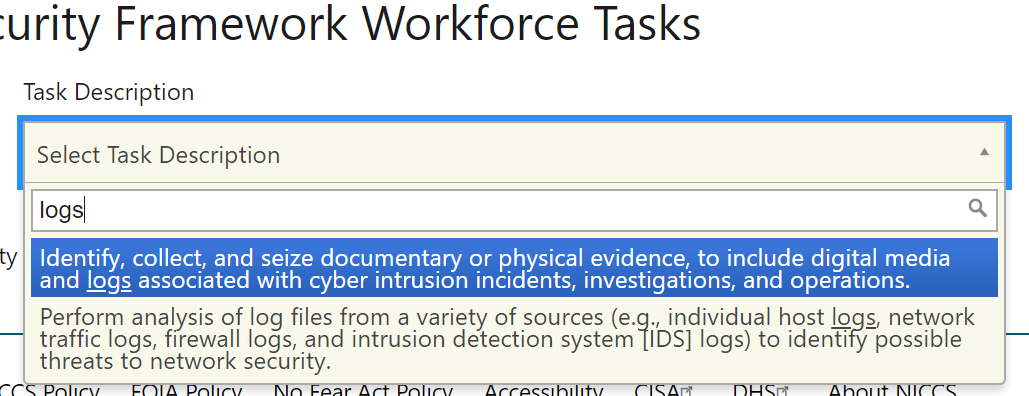
As an example, let’s say for a moment that we had an active need for someone to start consolidating all of the logs our organization generates and start sifting through them for important information on potential threats. If we were looking for someone through standard information security roles, we’d probably look for an SIEM Analyst (Security Information and Event Management). However, SIEM does not exist in the NICE Framework — indeed, quite a number of industry standard acronyms and terms do not exist in NICE at all, but more generic terms do.
This is one of the strengths of the NICE framework, since it brings all of the departments onto the same page in regards to terminology. For instance, someone in HR may have no idea what “assess the results of intrusion detection system scans” may mean, but they’ve got a much better chance of understanding “compile logs for possible threats.” Using the above link, we could therefore go to the Tasks list and start searching for “logs,” which gives us a couple of possible starting points.
Since we don’t actively have an active incident we are investigating and we are trying to be proactive at the present time, the second description is more along the lines of what we are looking for.
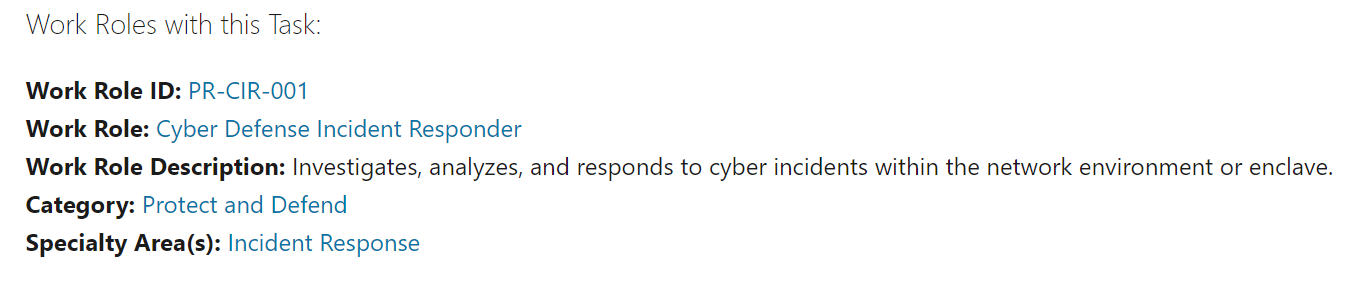
This gives us the NICE work role of Cyber Defense Incident Responder. Once we click on the link, it gives us a massive list of KSAs and tasks that the target employee would be requested to cover and be familiar with. We are also given a recommended list of experience and education levels for Entry Level requirements on up to Advanced.
Conclusion
Let's bring it back around to our initial restaurant analogy. The Excel spreadsheet is our take-out menu, with each of the categories being a particular cuisine. The specialty areas are our entrée types, and with the work roles we have our proteins added in which make it a full usable dish.
So we go from a top-level concept of looking for someone in cybersecurity, all the way down to the specific skill sets we need for a very particular job. We can then use this to help build out the job listings we need in a common language that works across multiple departments and multiple skill sets. This way, we don't end up with the right person stuck in limbo for weeks as an email chain goes back and forth asking, "Is this what we're looking for?"

Learn Network Forensics
Sources
- The NICE Cybersecurity Framework Explained, eLearn Security
- NICE Tutorials, NIST
- NICE Cybersecurity Workforce Framework, NICCS