Network security

Network security
Explore the essentials of Zero Trust Architecture, its impact on cybersecurity in 2024 and how it shapes modern digital security strategies.

December 19, 2023
Jeff Peters
Network security
Explore the vital role of network security protocols in safeguarding digital infrastructure in 2024, covering types, trends and best practices.

December 19, 2023
Infosec Institute
Network security
Learn how to approach asset mapping and detection.

December 14, 2023
Drew Robb
Network security
With a four-year deadline to meet, how will the military and defense sector respond to the Pentagon’s zero-trust mandate?

September 22, 2023
Drew Robb
Network security
Learn the basics of configuring a network firewall in this episode of Cyber Work Applied featuring Infosec Skills author Mike Meyers.

March 13, 2023
Bianca Gonzalez
Network security
When can a certain network utility do the most good for you? Learn how and when you can use Ping, Netstat, Traceroute and ARP in this video.

February 6, 2023
Bianca Gonzalez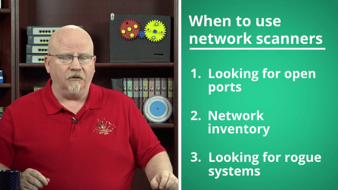
Network security
Learn how to use free network scanning tools like Nmap, Zenmap and Advanced Port Scanner in this episode of Cyber Work Applied.

January 2, 2023
Bianca Gonzalez
Network security
Security engineers utilize a range of tools to prevent cyber threats. These are the top 13 tools security engineering industry leaders are using now.

October 26, 2022
Dan Virgillito
Network security
Learn how to better understand the Zeek log file structure and how to use the logs when investigating events.

March 21, 2022
Mark Viglione
Network security
Learn about how to use Zeek, a free, powerful open-source network traffic analyzer.

March 7, 2022
Mark ViglioneLearn from the experts the processes behind cracking passwords, like:
- Capturing Windows Password Hashes
- Understanding Windows Passwords
- Cracking Windows Password Hashes with Cain and Abel
- Cracking Password Hashes with Rainbow Tables
In this series
- What is zero trust architecture (ZTA)? Pillars of zero trust and trends for 2024
- A deep dive into network security protocols: Safeguarding digital infrastructure 2024
- Asset mapping and detection: How to implement the nuts and bolts
- The Pentagon goes all-in on Zero Trust
- How to configure a network firewall: Walkthrough
- 4 network utilities every security pro should know: Video walkthrough
- How to use Nmap and other network scanners
- Security engineers: The top 13 cybersecurity tools you should know
- Converting a PCAP into Zeek logs and investigating the data
- Using Zeek for network analysis and detections
- Suricata: What is it and how can we use it
- Intrusion detection software best practices
- What is intrusion detection?
- How to use Wireshark for protocol analysis: Video walkthrough
- 9 best practices for network security
- Securing voice communications
- Introduction to SIEM (security information and event management)
- VPNs and remote access technologies
- Cellular Networks and Mobile Security
- Secure network protocols
- Network security (101)
- IDS/IPS overview
- Exploiting built-in network protocols for DDoS attacks
- Firewall types and architecture
- Wireless attacks and mitigation
- Wireless network overview
- Open source IDS: Snort or Suricata? [updated 2021]
- PCAP analysis basics with Wireshark [updated 2021]
- What is a firewall: An overview
- NSA report: Indicators of compromise on personal networks
- Securing the home office: Printer security risks (and mitigations)
- Email security
- Data integrity and backups
- Cost of non-compliance: 8 largest data breach fines and penalties
- How to find weak passwords in your organization’s Active Directory
- Monitoring business communication tools like Slack for data infiltration risks
- Firewalls and IDS/IPS
- IPv4 and IPv6 overview
- The OSI model and TCP/IP model
- Endpoint hardening (best practices)
- Wireless Networks and Security
- Networking fundamentals (for network security professionals)
- How your home network can be hacked and how to prevent it
- Network design: Firewall, IDS/IPS
- Work-from-home network traffic spikes: Are your employees vulnerable?
- RTS threshold configuration for improved wireless network performance [updated 2020]
- Web server protection: Web server security monitoring
- Web server security: Active defense
- Web server security: Infrastructure components
- Web server protection: Web application firewalls for web server protection
Phishing simulations & training
Unlock pricing and see how Infosec IQ can help you empower employees with 2,000+ security awareness resources to:
- Reduce security events
- Reinforce cyber secure behaviors
- Strengthen cybersecurity culture at your organization

