Backup Media Encryption
The problem
Information Security is like a chain: it is only as strong as its weakest link. You can protect your network with expensive firewalls, use auditing within your systems and use secure passwords. But what if the person responsible to take the backup tapes offsite drives home, stops at the supermarket one night and has their car broken into? What was on the tapes in their laptop bag? How easy is it to access that data? What impact does it have on the security of the organisation?

Learn Secure Coding Fundamentals
This example is not uncommon. Statistics in this area are very hard to come by, because victims of theft or simple loss of the vast amounts of data a single backup media could contain, would be very hesitant to report this. A tape could contain a backup of system files such as an Active Directory database from which password hashes can be obtained. It could contain confidential company data or a database with client details or even credit card details. As an example, Bank or America lost backup media in transit, containing details of 1.200.000 customers.
For this reason, compliance requirements by for instance HIPAA and PCI can also play a factor in the need to encrypt backup media.
The Solution
This is where encryption comes in. If the data written on the backup media is properly encrypted, it will be useless for anyone without the key.
Most backup software products have easy-to-use encryption options built into them. Some hardware providers have also added encryption solutions to their products. I will show and discuss some of these.
Hardware Solutions.
LTO
(linear Tape-Open) is a popular backup storage technology, developed by HP, IBM and Quantum and has been around since 1997. The latest model is the LTO-6 drive which has a native capacity of 2.5 TB. Since the LTO-4 model, drive level encryption has been added. The encryption is based on 256-bit AES-GCM. The LTO program claims this drive level encryption only adds about a 1% delay to data transfers.
DDS
(Digital Data Storage) has been around for a very long time. Its latest model, the DAT320 can provide hardware encryption at full speed. Just like the LTO system, it uses 256 AES-GCM.
RDX is a removable disk technology. It is based on an internal or external dock and media cartridges that contain a 2.5" SATA harddisk. The drive or dock itself cannot provide hardware encryption, but the company Imation has added the encryption process to the driver and the media itself. This product is called RDX Media Secure. It does not integrate with many backup applications however.
Software Solutions.
Symantec Backup Exec is the leader in backup software solutions based on market share. This product supports built-in software encryption as well as the hardware solutions such as the systems mentioned before. It allows for the selection of 256-bit AES or the slightly faster 128-bit AES (software only) algorithms. One benefit of the use of this software based data encryption is that any remote agents encrypt their data before sending it over the network to the backup server which will then put it on tape. This will protect the data during the transfer stage from any eavesdroppers.
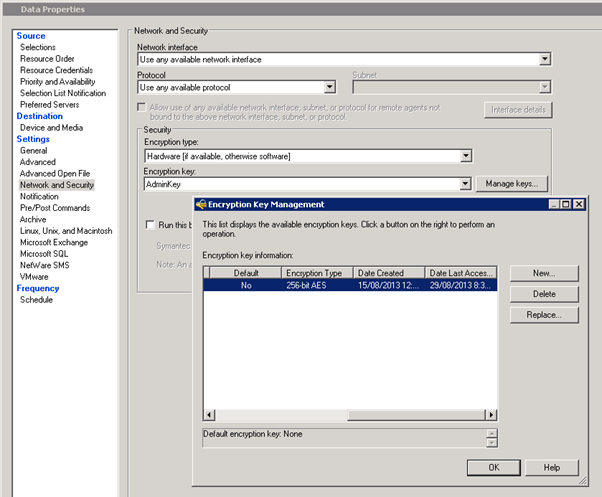
Encryption options in Symantec Backup Exec 2010 R3
StorageCraft Shadowprotect is an example of a backup product that works on a smaller scale. It supports the backup of volumes and VM's to disk. Especially full VM copies on an easily accessible external disk should be protected from loss or theft. The software allows for encryption in RC4 and AES in 128-bit and AES in 256-bit.
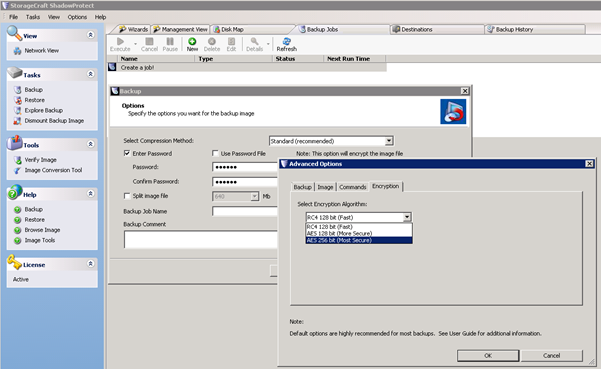
Encryption options in StorageCraft Shadowprotect
Performance
Some manufacturers claim very limited impact on backup transfer speeds when using their built-in hardware encryption system. In practice however, this impact can be significantly larger. This all depends on many variables. For instance, it is important to know if the data is located on the same physical server or if it needs to transferred through the network and at what speed. If the data comes in slow, the encryption process will have less of an impact on the overall speed of the backup. Also, even though the main share of the processing power required for the hardware encryption process is taken care of by the backup hardware itself, the CPU or the amount of RAM may still be a limiting performance factor.
I have done some basic testing of actual performance impact in several different situations and I have listed the findings in the following table.
These findings show that the hardware encryption on the LTO 4 and 5 drives are faster than the software encryption on the RDX drives. They are far from the theoretical 1% stated in the specifications however. Amazingly enough in one situation, the backup process was actually consistently faster after enabling hardware encryption. This could be purely a coincidence due to other external factors on the backup server or maybe due to a difference in timing of the backup stages. I have not found a clear reason yet. I guess it comes down to testing the implementation of media encryption before the implementation. There are too many factors to be able to easily predict the impact.
1
0
21
-15.0%
6
339
446
+5.5%
4
690
690
-21.3%
2
307
207
-20.4%
1
105
0
-12.7%
Encryption and Compression
An interesting dilemma arises when a combination between compression and encryption is to be used. The problem here is that encrypted data cannot be compressed as well as unencrypted data. When multiple remote sources are backed up through the network however, encryption is required to prevent an eavesdropper from acquiring the data. This is where software compression comes in. Software compression can be slower, but when this is used by a remote agent on a source server, the amount of data to be sent through the network will be reduced which in turn will relatively increase the transfer speed. The remote agent can then encrypt the data. Not only does this add a security control, it also adds integrity checks to the data. If the data has become corrupted or changed in transit, it will simply be impossible to decrypt the information.
Basically, this means that if you use software encryption, you need to enable software compression as well. Software compression will take place before software encryption, which will eliminate the limitation of compression ratios. Performance will be affected compared to hardware compression and encryption though.
Cloud-Based backup
A Cloud-Based backup is a good alternative solution. This method is getting more and more popular due to the faster connection speeds available and the relatively low pricing. Because there are no physical media involved, no physical media loss can happen. There is a small catch however. It is still important to encrypt the backup data. This will prevent any eavesdropper from intercepting the backup during the upload process or while it is stored. Fortunately providers such as Amazon, Mozy, Terremark, Norton and most others can provide an encryption service.
The Risks
Like any security control, backup media encryption also has its weaknesses. Considering AES-256 is pretty much the standard in most backup applications, a bruteforce or dictionary attack can be ruled out if the passphrase used is of a sufficient strength. There is always the risk of a systems administrator using the same password for the encryption process as for another service which is much easier to compromise. The attacker can try the compromised password on the encrypted data.
Another risk is the theft of the entire backup server (which could even have a tape in the drive at that moment). The server contains the key used to encrypt, so it can easily decrypt the data on tape again. Apart from this physical access to the server, an attacker could also gain remote access to the backup server, leading to the same results, although the download of the data might cause some headaches for the attacker in that case.

Intro to x86 Disassembly
These risks are easily avoided though, so if time and equipment allow for the use of Backup Media Encryption, there is nothing really holding back its implementation.







