CMMC vs. NIST 800-171
In recent times, the US Department of Defense (DoD) has taken more stringent measures to assess and enhance the cybersecurity posture of the Defense Industrial Base (DIB). In response to the continued exfiltration of controlled unclassified information (CUI) from its supply chain, the Cybersecurity Maturity Model Certification (CMMC) was created. Its purpose is to ensure that all contractors and subcontractors meet minimum security standards, according to their role.
Until now, the defense supply chain providers have been used to self-certifying under the NIST SP 800-171. They are now faced with more rigorous requirements and third-party certification that can ensure better safety of data in a company's computing environment. Contractors and subcontractors will be also required to detect and report cyber incidents on Covered Contractor Information Systems (CCISs) featuring Covered Defense Information (CDI) or Controlled Technical Information (CTI).
In accordance, CMMC v1.0 is a step forward in compliance fulfilment in providing federal agencies with security requirements for protecting CUI in nonfederal systems and organizations. What’s more, CMMC builds upon existing regulation DFARS 252.204-7012 in the protection of CDI, including CTI, to ensure that appropriate cybersecurity controls are in place. These controls will appropriately protect the systems where unclassified information owned or operated by a contractor resides.

Learn ICS/SCADA Security Fundamentals
Do CMMC or NIST 800-171 apply to me?
The short answer is yes. That said, it’s important to know how CMMC has evolved from the current NIST 800-171 standard, which is a big change to cybersecurity governance regulations.
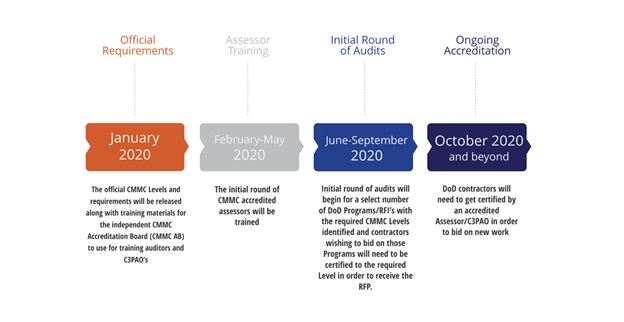
On January 30, 2020, the DoD released CMMC, which was intended to replace NIST 800-171 compliance across the DIB and remedy the issue of non-compliance of some vendors. In past years, primary contractors or subcontractors have struggled to implement specific security measures, assess and report their progress while having already been awarded a defense contract and entrusted with the handling of sensitive data.
The CMMC is the DoD's means to combat the incredible number of cyberthreats directed to the DIB and respond to significant compromises of sensitive defense information located on contractors' information systems. This unified standard for DoD acquisitions will expand cybersecurity requirements to contractors and their supply chains for the purpose of reducing the impact of advanced persistent threat (APT) attacks.
Who is required to certify under CMMC? Basically, all defense contractors and subcontractors, including US and foreign suppliers of any size, will need to be compliant and certified before the contract is officially awarded. Part of the process of becoming compliant with this regulation is to safeguard handling CUI (i.e., information the government creates or possesses) in the Federal Contract Information (FCI) environment.
Bear in mind that the “CMMC applies to only a DIB contractor’s unclassified networks that handle, process, and/or store FCI or CUI,” as stated by the Office of the Under Secretary of Defense for Acquisition & Sustainment. The OUSD(A&S) sought the development of an approach that would help with the System Security Plan (SSP) and Plan of Action & Milestones (POA&M); “[these] are requirements for NIST 800-171 compliance, so lacking these documents will be considered non-compliant that could have significant negative consequences (e.g., False Claims Act (FCA) violation,” says ComplianceForge.
What does CMMC look like?
The CMMC model is a tiered approach to audit contractor compliance in cybersecurity. It has five levels of maturity expectations, which range from basic cyber hygiene to advanced concepts, and each has its own number of controls that are needed to be reviewed in a CMMC audit.
Regulations have been nested into the CMMC Framework. This consists of 17 domains in which cybersecurity is ensured through a number of capabilities. In turn, the latter comprises practices and processes that allow a company to achieve a certain capability. To achieve compliance with CMMC Level 3, suppliers need to comply with NIST 800-171 level of practices.
The CMMC domains are inherited from earlier frameworks. NIST SP 800-171 had a reduced number of domains — 14. These domains form what is considered to be the foundation on which to build a general security plan able to withstand emerging cyber threats.
How CMMC differs from NIST 800-171
While CMMC is based on much of NIST 800-171, there are some obvious differences. It is important to understand them both and know which applies to your DoD contracting or subcontracting.
The CMMC is the new third-party assessment requirement. Unlike NIST SP 800-171, which required DoD contractors to self-certify to either be compliant or to be taking concrete steps towards compliance, CMMC makes provisions for third-party assessment organizations (C3PAOs) to analyze the company and assign a maturity level based on the state of its cybersecurity program. 1 is the lowest rating and 5 is the highest rating.
No delayed compliance! Effective in June 2020, selected RFIs (Requests for Information) will refer to CMMC requirements, and in September 2020, selected RFPs (Requests for Proposals) will include CMMC requirements that must be met by the time the contract is awarded.
CMMC has also some good news for smaller contractors. In fact, the smaller the supplier the smaller the requirements to be met. Some smaller companies, sooner or later, will be able to comply only at level 1 (basic cyber hygiene — 17 practices) or level 2 (intermediate cyber hygiene — 72 practices), with only fewer much larger companies having to comply with level 5 (advances/progressive — 171 practices).
The focus of the two document designations used by the DoD are also different. In addition to the normal important aspects of domains representing security areas, access control, personnel security, auditing practices and so on, the CMMC takes into consideration situational awareness, cyber threat intelligence and threat hunting, which these topics have become more and more important lately to catch issues sooner after their onset.
How to certify
Bear in mind that without a valid CMMC certification (Level 1 through 5), the prime and/or subcontractor will be barred from the contract. Therefore, providing assessments to the estimated 300,000 defense contractors will definitely be a mammoth task.
Because self-certification will not be permitted, the DoD has gone on to provide initial training guidance to the Cybersecurity Maturity Model Certification Accreditation Body (CMMC-AB) in January 2020, at which time an initial round of accredited CMMC Third Party Assessment Organizations (C3PAOs) and individual assessors trained and tested will evaluate companies’ CMMC levels.
CMMC-AB had the goal to license up to 10,000 assessor candidates between February and May, and with more than 300,000 defense suppliers, this means a large number of assessors will still be needed. The CMMC-AB plans to include a list of approved C3PAOs to schedule a CMMC assessment for a specific level. To minimize wait time and issues, DIB companies are encouraged to complete a self-assessment prior to scheduling a CMMC assessment.
Note: If a DIB company does not possess CUI, then they do not require a CMMC certification. As for the level of the CMMC certificate, it is dependent upon the type of information circulated down from a prime contractor.
When it comes to contracts that require CMMC, the cost of certification will be considered an allowable, reimbursable cost (i.e., expenses specified in a contract that can be billed to the DoD) which are not to be prohibitive. As for the CMMC assessment costs, it will depend upon several factors, including to which level the certification is needed.
DoD intends to roll out the CMMC in phases
“CMMC is to be rolled out gradually and will eventually replace NIST 800-171 compliance,” writes Corserva, a leading IT solutions provider. However, there will be a period where both NIST 800-171 and CMMC will be in effect at the same time — so, look for overlapping compliance elements; and by 2026, all new DoD contracts will require CMMC. Those leveraging the steps to be compliant, for example, can use Corserva’s experts, who can help one learn how to comply with NIST 800-171 and CMMC then be given a plan describing a timeline and costs for them to achieve compliance.

Learn Vulnerability Assessments
Conclusion
Securing the DoD information involves ensuring protection of the data present on the DIB networks, which are often not as heavily protected as official government systems. In the past few years, the DoD has established a number of programs to increase the resiliency of its contractors and partners. In 2013, for example, DoD made the DIB Cybersecurity and Information Assurance (CS/IA) program permanent “to enhance and supplement DIB participants’ capabilities to safeguard DoD information that resides on, or transits, DIB unclassified networks or information systems.” The program included information sharing on cyberthreats, mitigation measures and best practices.
Today, a new program promises to further secure the information entrusted to vendor’s IT networks. Any business that is awarded a DoD contract or has a subcontract must adopt the cybersecurity standards outlined in the CMMC model. Unlike NIST 800-171 where the contractors could perform a self-assessment, now with CMMC, a third-party audit is needed. This means that a great number of assessors will be needed in the next few years in order to quickly certify potential winners of DoD contracts. Therefore, interested professionals should look for a good number of CMMC jobs to become available.
Sources
- Cybersecurity Maturity Model Certification (CMMC) Version 1, OUSD A&S
- CMMC FAQ's, OUSD A&S
- CMMC Academy, Celerium Inc.
- CMMC Compliance Guide, Compliance Forge, LLC.
- NIST 800-171 vs CMMC 1.0, LinkedIn
- NIST Compliance and CMMC, Corserva
- CMMC 1.0 vs. NIST 800-171 – Eight Essential Differences, Breaking Defense
- Cybersecurity Maturity Model Certification (CMMC) Assessor job, Lensa, Inc.
- FACT SHEET: Defense Industrial Base (DIB) Cybersecurity Activities, DoD CIO
- CMMC (Cybersecurity Maturity Model Certification) Accreditation Body, cmmcab.org
- NIST Updates SP 800-171 to Help Defend Sensitive Information from Cyberattack, nist.gov
- From NIST 800-171 to CMMC: A Comprehensive Defense Compliance Guide, RSI Security
- 7 Steps To An Audit-Ready Cybersecurity Maturity Model Certification (CMMC) Program, Compliance Forge, LLC.
- The Cybersecurity Maturity Model Certification explained: What defense contractors need to know, CSO