Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
Security awareness training buyer’s guide

Security awareness tip sheets

Security Awareness Posters
Security Awareness Training as a Key Element in Security Culture Change

Marine Lowlifes Security Awareness Posters
Download the Infosec Skills Course Catalog

Infosec IQ training module catalog

How to secure your software faster and better ebook
Hacked for the Holidays Toolkit

Free poster kit: Work Bytes

Developing cybersecurity talent and teams: Experts weigh in on building effective training plans and creating stronger teams

Cybersecurity Maturity Model Certification (CMMC) ebook

Cybersecurity Interview Tips ebook
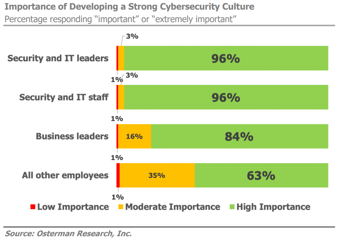
Cybersecurity Culture — Quantified

CompTIA Security+ 701: How the world's most popular cert is changing in 2024
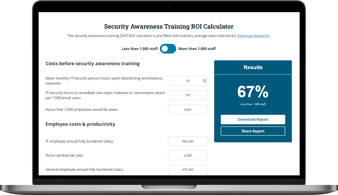
Calculate the ROI of security awareness at your organization

Ransomware demonstration: How ransomware infects a system

How to use Wireshark for protocol analysis | Cyber Work Applied

How an SQL injection attack works | Cyber Work Applied

How to set up a man in the middle attack | Cyber Work Applied
Write a port scanner in Python in 5 minutes | Cyber Work Applied

How cross-site scripting attacks work | Cyber Work Applied
Inside Equifax's massive breach | Cyber Work Applied

Cryptography basics: How does encryption work? | Cyber Work Applied