Strengthen workforce readiness with free resources
Whether you're building team capability, closing skill gaps or preparing your workforce for certification, our resource center has the tools, guides and expert insights to support your program.
Featured content

Cybersecurity talent development playbook
Upskill your security team with 12 pre-built, role-guided training plans that are vetted by experts and mapped to skills requested by employers.
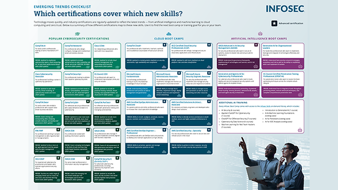
Emerging trend infographic: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free infographic.

Agentic AI workshop: Train your first cybersecurity model in 90 minutes
Join Keatron Evans, a 20-year cybersecurity veteran and Infosec’s VP of Portfolio Product and AI Strategy, for a unique workshop on combining your cyber skills with the latest AI capabilities.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.