What's included
Everything you need to know
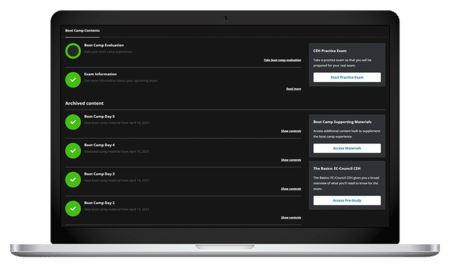
- 90-day extended access to Boot Camp components, including class recordings
- 100% Satisfaction Guarantee
- Exam Pass Guarantee
- Exam voucher
- Free 90-day Infosec Skills subscription (access to 1,800+ additional courses and labs)
- Hands-on cyber ranges and labs
- Knowledge Transfer Guarantee
- Onsite proctoring of exam
- Pre-study learning path
- Unlimited practice exam attempts
Syllabus
Training schedule
Day 1
Introduction to Red Team Operations
Setting objectives
Reconnaissance
Optional group & individual study
Schedule may vary from class to class
Day 2
Reconnaissance continued
Target identification
Optional group & individual study
Schedule may vary from class to class
Day 3
Gaining access
Establishing foothold and maintaining presence
Optional group & individual study
Schedule may vary from class to class
Day 4
Establishing foothold and maintaining presence continued
Completing objectives
Optional group & individual study
Schedule may vary from class to class
Day 5
Reporting
Additional Red Team Operations resources
CRTOP exam review and prep
Take the CRTOP exam
What makes the Infosec Red Team Operations prep course different?
You can rest assured that the Red Team Operations training materials are fully updated and synced with the latest version of the exam. With 20 years of training experience, we stand by our Red Team Operations training with an Exam Pass Guarantee. This means if you don’t pass the exam on the first attempt, we’ll pay for your second exam at no additional cost to you!
Infosec success stories

"The team at Infosec was great from the start, and they were as excited about my journey as I was. They explained the value behind each training I was considering and how it could further my goals. Their enthusiasm was a great motivation throughout the boot camp."
Elle Autumn
EC-Council Certified Ethical Hacking Course: CEH Certification Training Boot Camp Read Elle's Story
"Infosec has uniquely prepared me for any CMMC retraining that will take place inevitably in the future. With them, it’s not just about completing the certification; it's about being a true contributor to the ecosystem."
James Ahern
Certified CMMC Assessor (CCA) Boot Camp Read James's Story
"The hands-on training was the best part. You have an instructor you can actually reach out to and ask questions — not only on the material, but also about things out in the wild with cybersecurity."
Eddie Quinones
CompTIA Security+ Certification Training Boot Camp Read Eddie's Story
"The Infosec CISM Boot Camp gave me the ability to intelligently explain why I'm making a decision. Ultimately, the C-suite is happy and they know, 'Hey, here's a person that we can rely on."
Mohammad Mirza
ISACA Certified Information Security Manager (CISM) Training Boot Camp Read Mohammad's StoryGuaranteed results
Our boot camp guarantees
Exam Pass Guarantee
If you don’t pass your exam on the first attempt, get a second attempt for free. Includes the ability to re-sit the course for free for up to one year (does not apply to CMMC-AB Boot Camps).

100% Satisfaction Guarantee
If you’re not 100% satisfied with your training at the end of the first day, you may withdraw and enroll in a different online or in-person course.

Knowledge Transfer Guarantee
If an employee leaves within three months of obtaining certification, Infosec will train a different employee at the same organization tuition-free for up to one year.
Who should attend

This intensive boot camp is designed for individuals with various backgrounds and roles in the field of cybersecurity. The following professionals will significantly benefit from our comprehensive training:
- Red team members and offensive security specialists
- Penetration testers, security researchers and ethical hackers
- Incident responders
- CISOs and security managers
- Security and network architects, engineers and administrators
- Professionals responsible for physical and information security
Attending this boot camp gives you practical knowledge, hands-on experience and industry-relevant skills vital for excelling in red team operations and offensive security. The certification you obtain validates your expertise and prepares you to identify and mitigatigate security risks before they happen.
Before your Boot Camp
Prerequisites
What's next?
After you finish the boot camp

After completing the Red Team Certification Training Boot Camp, you’re on your way to being a Certified Red Team Operations Professional.
With cyberattacks on the rise, public and private organizations want to ensure their data is safe behind their firewalls. But to truly test their security, they’ll need people who have red team certification training. Common job titles that may have CRTOP certification are:
- Red team specialist
- Penetration tester
- Security consultant
- Security engineers
- Security managers
These are just a few examples of job opportunities that you could get with a red team operations certification. The specific job titles and roles may vary depending on the organization and industry.
Exam Prep
What are some tips for preparing for the CRTOP exam?
Our best tip is to enroll in an exam training course, such as our red team training program, which provides comprehensive preparation and guidance tailored to the CRTOP certification. It’s also important to practice! That’s why we offer practice exams and hands-on exercises in our cyber ranges to reinforce your red teaming knowledge and skills.
Exam Process
How does the CRTOP examination process work?
The Certified Red Team Operations (CRTOP) body of knowledge consists of seven domains covering the responsibilities of a red team member. The certification exam is a 50-question, traditional multiple-choice test. Questions are randomly pulled from a master list and must be completed in two hours. The seven CRTOP domains are:
- Red team roles and responsibilities
- Red team assessment methodology
- Physical reconnaissance tools and techniques
- Digital reconnaissance tools and techniques
- Vulnerability identification and mapping
- Social engineering
- Red team assessment reporting
Career Opportunities
What are the career opportunities like for OWASP certified professionals?
With cyberattacks on the rise, public and private organizations want to ensure their data is safe behind their firewalls. But to truly test their security, they’ll need people who have red team certification training. Common job titles that may have CRTOP certification are:
- Red team specialist
- Penetration tester
- Security consultant
- Security engineers
These are just a few examples of job opportunities that you could get with a red team operations certification. The specific job titles and roles may vary depending on the organization and industry.
What job titles are most common for people with a Red Team Operations certification?
Some common positions that this certification can help you land include:
-

Security manager
-

Security and network architect
-

Penetration tester
-

Red team specialist
FAQ
Frequently asked questions
What is the purpose of red team training?
What can I expect to learn in red team training?
What does a red team operator do?
What are red team skills?
It’s not just being good with computers. red team skills encompass a range of technical and non-technical abilities. Some of the best red team operators have skills including proficiency in penetration testing methodologies, vulnerability assessment, social engineering, exploit development and evasion techniques.
Plus, to be a sought-after red team operator, you should have a strong knowledge of operating systems, networking protocols and security tools. Additionally, red team professionals need critical thinking, problem-solving and communication skills to effectively identify, exploit and communicate security vulnerabilities to stakeholders.
Average Salary
CRTOP certification salary expectations
CRTOP professionals earn competitive salaries. However, exact salaries vary based on experience, location, industry and job title. The average red team certification salary is $111,529 annually, with the possibility of earning more.
Award-winning training you can trust




No available dates
We're sorry, but Red Team Operations Certification Training Boot Camp does not have any scheduled dates. However, we’d love to help you get the specialized training you need. Book a meeting with a representative today to discuss setting up a course.
Why choose Infosec?
Category
Infosec logo
SANS Institute
Training Camp
Global Knowledge (Skillsoft)
AI-powered, hands-on skill validation
12 Roles
Integrated for all roles
90 days
*Protects your investment if trained employees leave within three months of obtaining certification (Infosec will train a different employee at the same organization tuition-free for up to one year).