
What's included
Everything you need to know
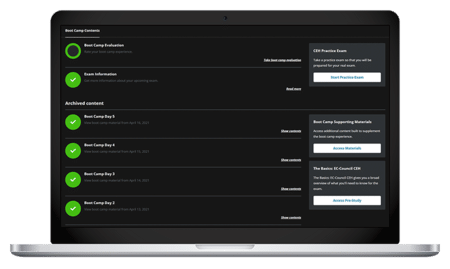
- 90-day extended access to Boot Camp components, including class recordings
- 100% Satisfaction Guarantee
- Free 90-day Infosec Skills subscription (access to 1,800+ additional courses and labs)
- Hands-on cyber ranges and labs
- Knowledge Transfer Guarantee
- Pre-study learning path
Syllabus
Training schedule
Day 1
Introduction
Incident response process (i)
Incident response process (ii)
Optional group & individual study
Schedule may vary from class to class
Day 2
Events & incident detection (i)
Events & incident detection (ii)
Optional group & individual study
Schedule may vary from class to class
Day 3
Triage & analysis (i)
Triage & analysis (ii)
Optional group & individual study
Schedule may vary from class to class
Day 4
Incident management knowledge base (i)
Incident management knowledge base (ii)
Optional group & individual study
Schedule may vary from class to class
Day 5
Incident response
Course materials review
What makes the Infosec Incident Response & Network Forensics prep course different?
You can rest assured that the Incident Response & Network Forensics training materials are fully updated and synced with the latest version of the exam. With 20 years of training experience, we stand by our Incident Response & Network Forensics training with 100% satisfaction guaranteed. This means if you’re not 100% satisfied with your training at the end of the first day, you may withdraw and enroll in a different online or in-person course.
Infosec success stories

"The team at Infosec was great from the start, and they were as excited about my journey as I was. They explained the value behind each training I was considering and how it could further my goals. Their enthusiasm was a great motivation throughout the boot camp."
Elle Autumn
EC-Council Certified Ethical Hacking Course: CEH Certification Training Boot Camp Read Elle's Story
"Infosec has uniquely prepared me for any CMMC retraining that will take place inevitably in the future. With them, it’s not just about completing the certification; it's about being a true contributor to the ecosystem."
James Ahern
Certified CMMC Assessor (CCA) Boot Camp Read James's Story
"The hands-on training was the best part. You have an instructor you can actually reach out to and ask questions — not only on the material, but also about things out in the wild with cybersecurity."
Eddie Quinones
CompTIA Security+ Certification Training Boot Camp Read Eddie's Story
"The Infosec CISM Boot Camp gave me the ability to intelligently explain why I'm making a decision. Ultimately, the C-suite is happy and they know, 'Hey, here's a person that we can rely on."
Mohammad Mirza
ISACA Certified Information Security Manager (CISM) Training Boot Camp Read Mohammad's StoryGuaranteed results
Our boot camp guarantees

100% Satisfaction Guarantee
If you’re not 100% satisfied with your training at the end of the first day, you may withdraw and enroll in a different online or in-person course.

Knowledge Transfer Guarantee
If an employee leaves within three months of obtaining certification, Infosec will train a different employee at the same organization tuition-free for up to one year.
Who should attend

The Incident Response Training & Network Forensics Boot Camp is ideal for a wide range of professionals looking to enhance their skills in incident response and network forensics. Here’s who will benefit most from this training:
- Incident response professionals
- Network and system administrators
- Computer security incident response team (CSIRT) members
- Anyone interested in improving their network forensics and incident management skills
By attending the Incident Response Training and Network Forensics Boot Camp, you gain the necessary expertise to excel in incident response, network forensics and cybersecurity, making you an asset to your organization. Expand your professional skill set and stay ahead in the ever-evolving field of cybersecurity with our top-tier network forensic and incident response training.
Before your Boot Camp
Prerequisites
What's next?
After you finish the Incident Response Training and Network Forensics Boot Camp

After completing this boot camp, you're on your way to taking your career to the next level. Here are some responsibilities associated with this training:
- Be responsible for detecting and responding to security incidents, investigating cyber threats and implementing incident response strategies to mitigate risks.
- Specialize in analyzing network traffic, identifying security breaches and conducting digital investigations to gather evidence for legal proceedings.
- Provide expert guidance and recommendations to organizations on strengthening their cybersecurity posture, incident response planning and network forensics practices.
- Monitor and analyze security events and incidents, respond to alerts and perform investigations to identify and mitigate potential threats.
- Oversee a group of incident response professionals, coordinate response efforts and develop incident response strategies and protocols for the organization.
Exam Prep
What are some tips for preparing for this Incident Response and Network Forensics boot camp?
When you enroll in this boot camp, you’ll gain immediate access to an in-depth prep course to prepare for the boot camp and get the most out of your live experience. In addition, you’ll receive 90 days of access to all the content in Infosec Skills so you can continue to learn and build your skills after your boot camp ends. By enrolling, you’ll have everything you need to succeed before, during and after your live incident response training.
Career Opportunities
What are the career opportunities like for Incident Response and Network Forensics certified professionals?
Building your incident response and network forensics skills opens a range of exciting career options in the cybersecurity field. Here are some of the job titles commonly associated with this training:
- Network forensics investigator
- Cybersecurity consultant
- Security operations center (SOC) analyst
These job titles and responsibilities can vary depending on the organization, industry and specific role within the IT and cybersecurity field, but rest assured, you'll be well-equipped to pursue these exciting career paths and contribute to the security and resilience of organizations.
What job titles are most common for people with a Incident Response & Network Forensics certification?
Some common positions that this certification can help you land include:
-

Incident response team lead
-

Security operations center (SOC) analyst
-

Incident response analyst
FAQ
Frequently asked questions
What is incident response training?
What skills do you need to be an incident responder?
To excel as an incident responder, essential skills include a strong foundation in cybersecurity principles, technical expertise in areas like network protocols and operating systems, the ability to handle and respond to security incidents promptly, knowledge of digital forensics techniques, effective communication and collaboration skills, problem-solving abilities and a commitment to continuous learning and professional development.
These skills enable incident responders to effectively analyze, contain and remediate security incidents while minimizing the impact on organizations.
What do you need to be an incident responder?
To be an adept incident responder, you must possess a strong technical knowledge base, including a deep understanding of computer networks, operating systems and cybersecurity principles. Expertise in incident response methodologies, frameworks and procedures is essential. This involves being well-versed in incident detection, containment, eradication and recovery and utilizing incident handling tools, forensic techniques and evidence preservation methods.
Effective communication and collaboration skills are vital for incident responders. You need to communicate clearly with team members, stakeholders and external parties involved in incident response efforts. Collaborating effectively with others helps you coordinate response actions and share critical information. Operating as part of a team is crucial, as many incident responses cannot be completed by one person.
Average Salary
Incident Response certification salary expectations
Incident response professionals earn competitive salaries. While exact salaries vary based on experience, location and industry, incident response professionals earn an average of $83,000 annually, according to Payscale.
Award-winning training you can trust




Why choose Infosec?
Category
Infosec logo
SANS Institute
Training Camp
Global Knowledge (Skillsoft)
AI-powered, hands-on skill validation
12 Roles
Integrated for all roles
90 days
*Protects your investment if trained employees leave within three months of obtaining certification (Infosec will train a different employee at the same organization tuition-free for up to one year).