Phishing attack types
Prepare employees for every phishing tactic and deliver training to phished learners based on the attack type they click.

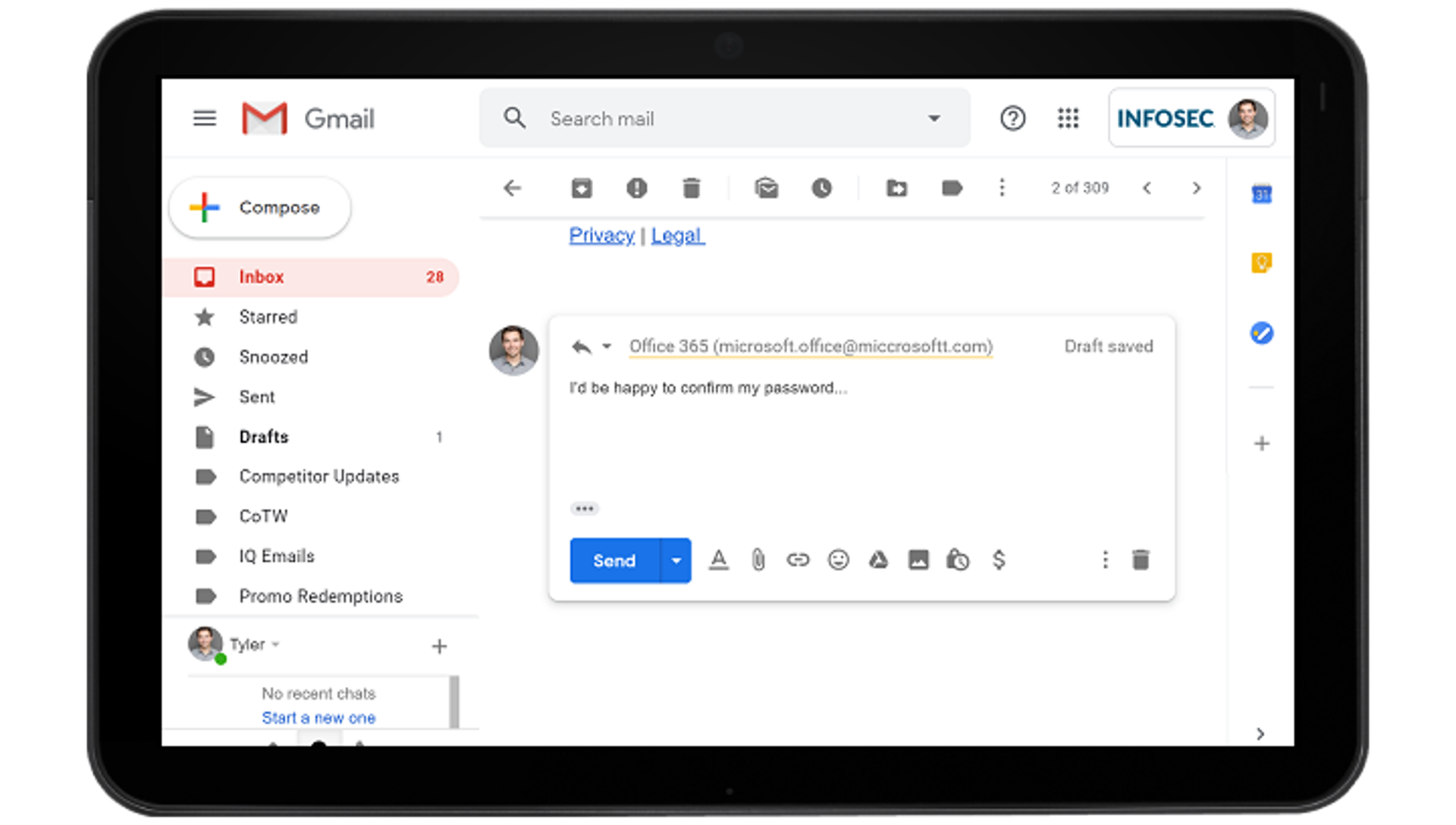
Phishy Domains & spoofing
Teach your employees the importance of domain verification on every email. Send simulated phishing emails from our library of Phishy Domains™ or add your own to typosquat domains familiar to your employees.
Replicate common domain spoofing techniques with our pre-built landing pages or add custom spoofed domains to provide an additional challenge for employees.
Email reply tracking
Enable reply tracking to learn each employee’s susceptibility to credential phishing and social engineering attacks and deliver training accordingly.
PhishSim reply tracking can report whether an employee replied, detect patterns such as credit card, bank account and Social Security numbers or store the entire reply for up to 14 days.