Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

How to Use Windows 10 Action Center and Security & Maintenance App for Hardening

Setting up a virtual lab for cybersecurity data science

Data Security in Windows 10: NTFS Permissions (Standard)
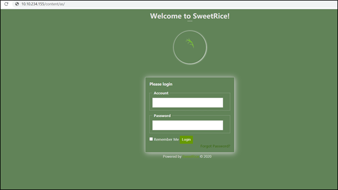
LazyAdmin: CTF walkthrough

CloudGoat walkthrough series: Cloud Breach S3
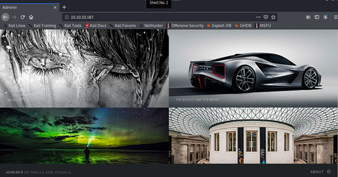
Hack the Box (HTB) machines walkthrough series — Admirer

Top 6 ransomware strains to watch out for in 2020

Common vulnerability assessment types

Common security threats discovered through vulnerability assessments
Octopus Scanner malware: What it is, how it works and how to prevent it | Malware spotlight

Cybersecurity Weekly: Software skimmer, Android app flaws, Google ad phish

How to Mitigate Poor HTTP Usage Vulnerabilities

How to Exploit Poor HTTP Usage

Introduction to HTTP (What Makes HTTP Vulnerabilities Possible)

Hack the Box (HTB) machines walkthrough series — Blunder

CloudGoat walkthrough series: IAM privilege escalation by rollback

CGEIT certification exam details and process [updated 2021]

Working with CloudGoat: The “vulnerable by design” AWS environment

How to Mitigate Integer Overflow and Underflow Vulnerabilities

How to exploit integer overflow and underflow

How to mitigate Credential Management Vulnerabilities

6 benefits of cyber threat modeling
WastedLocker malware: What it is, how it works and how to prevent it | Malware spotlight

How To Exploit Credential Management Vulnerabilities