Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
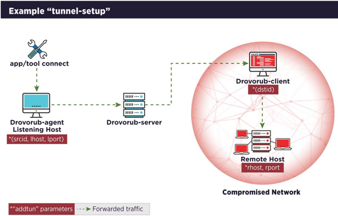
Drovorub malware: What it is, how it works and how to prevent it | Malware spotlight

What is the difference between the NICE framework and DoDD 8140/8570?

Cybersecurity Predictions For 2021

Phishing domain lawsuits and the Computer Fraud and Abuse Act

What is a vulnerability disclosure policy (VDP)?

MITRE Shield: An active defense and adversary engagement knowledge base

SO SIMPLE 1: CTF walkthrough

Comparing endpoint security: EPP vs. EDR vs. XDR

Top 6 JavaScript plugin security risks

Cybersecurity Weekly: New SolarWinds backdoor found, affects Microsoft and VMWare

Email-based attacks with Python: Phishing, email bombing and more

Attacking Web Applications With Python: Recommended Tools

Attacking Web Applications With Python: Exploiting Web Forms and Requests

Security tool investments: Complexity vs. practicality

Role and purpose of threat modeling in software development
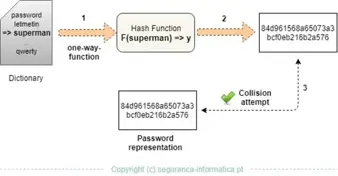
Hashcat tutorial for beginners [updated 2021]

Attacking Web Applications With Python: Web Scraper Python

Python for Network Penetration Testing: Best Practices and Evasion Techniques

5 changes the CPRA makes to the CCPA that you need to know

Python for network penetration testing: Hacking Windows domain controllers with impacket Python tools

How to hack a phone charger

Phishing: Reputational damages
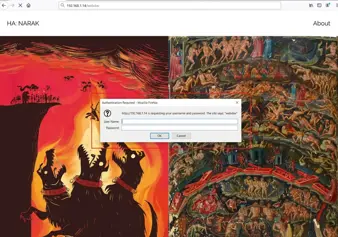
HA: Narak CTF walkthrough

Securing the home office: Printer security risks (and mitigations)