Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Increasing security by hardening the CI/CD build infrastructure

ATP group MontysThree uses MT3 toolset in industrial cyberespionage

Pros and cons of public vs internal container image repositories
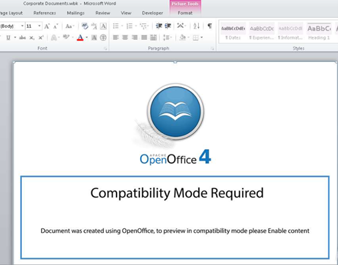
Cybersecurity Weekly: Exchange malware, Trickbot surges, new Nim malware

CI/CD container security considerations
Bandook malware: What it is, how it works and how to prevent it

Quantum cyberattacks: Preparing your organization for the unknown

Vulnerability scanning inside and outside the container

An Introduction to asymmetric vs symmetric cryptography

How Docker primitives secure container environments

Top 4 Zapier security risks

Common container misconfigurations and how to prevent them

Hack the Box (HTB) machines walkthrough series — Teacher

Worst passwords of the decade: A historical analysis

Building container images using Dockerfile best practices

Securing containers using Docker isolation

Introduction to container security

Commercial off-the-shelf IoT system solutions: A risk assessment

Most common MITRE ATT&CK tactics and techniques: CISA shares most common RVAs

Breaking misused stream ciphers

Entropy calculations

Top 8 Microsoft Teams security issues

Blockchain and hash functions

A school district's guide for Education Law §2-d compliance