Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Cybersecurity Weekly: Zero-Trust security, Android banking malware and security nihilism

5 tactics to improve cybersecurity hiring results

Average CGEIT Salary in 2022

Top 9 effective vulnerability management tips and tricks

Armaan Kapoor: Developer protégé turned cyber professional and social impact advocate

How to remove ransomware: Best free decryption tools and resources

JANGOW: 1.0.1: CTF walkthrough

Cybersecurity Weekly: UPS attack warning from CISA and DOE, Lapsus$ hacker group takedown and a surprising new text scam

SOC integration: Creating a well-built portfolio vs. a frankenstack

Can I make six figures working in tech? Here are the best tech jobs for 2022

Cybersecurity hiring: Why employer and higher ed collaboration is key

Infosec Scholarship winner profile: LaNeyshia Drew

Ransomware penetration testing: Verifying your ransomware readiness
Purple Fox rootkit and how it has been disseminated in the wild
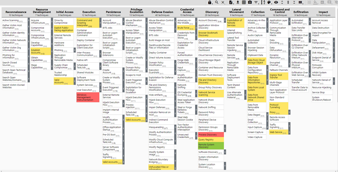
How to use MITRE ATT&CK Navigator: A step-by-step guide

Cybersecurity Weekly: Password phishing via BitB, current events phishing scams and increased need for cyber pros

After certification: Investing in employees' cybersecurity career pathways

Where do ransomware, cyber education and cyber insurance intersect?

Degree vs. certification: Best path to become a cybersecurity analyst

Cybersecurity analyst job description

Deadbolt ransomware: The real weapon against IoT devices

How to find the perfect security partner for your company
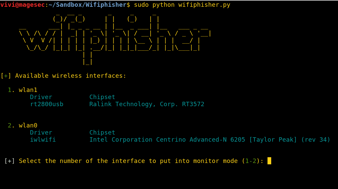
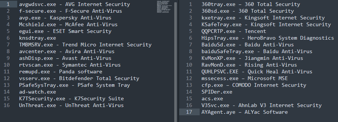
Red Teaming: Main tools for wireless penetration tests

Cybersecurity Weekly: Dodging MFA, struggles implementing zero-trust and tax season fraud concerns