Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Top 5 cybersecurity questions for small businesses answered

How does encryption work? Examples and video walkthrough

The most dangerous vulnerabilities exploited in 2022

Data architect: The ultimate career guide

Security operations center: 5 key functions your SOC should perform

The ultimate guide to ISACA certifications: Overview & career paths [updated 2022]

Cybersecurity Weekly: Cisco breach, Starlink hacked, Microsoft phishing attack targets crypto

I failed IAPP’s CIPP/C certification. Here’s how I recovered

What Is zero-trust security, and should your business adopt it?

Follina — Microsoft Office code execution vulnerability

Spring4Shell vulnerability details and mitigations

SOC analyst resume tips [updated 2022]

Cybersecurity Weekly: Emergency alert system, semiconductor ransomware, Slack password hashing bug fixed

What’s next in cybersecurity: Predictions from Andrew Howard

How training employees about ransomware can mitigate cyber risk
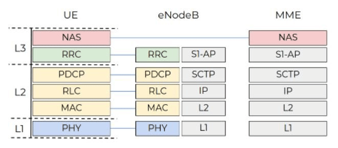
How to hack mobile communications via Unisoc baseband vulnerability
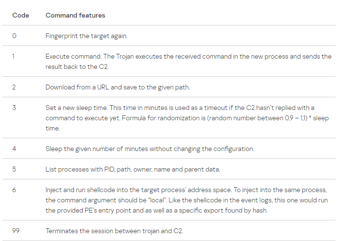
Fileless malware uses event logger to hide malware

Cybersecurity Weekly: Data breach cost passes $4MM, Uber data breach coverup, Chrome extension vulnerability
Infosec Skills August Challenge

Today’s IT job market: Beyond fear, uncertainty and doubt

Capture: Improve IoT firmware security with new firmware architecture

How learning to be "Always Flexible" helped a Marine in earning the Security+ certification

Nerbian RAT Using COVID-19 templates

Popular evasion techniques in the malware landscape