Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Handy Devices Revolution: Handy Pentesting & Hacking Part 1

Domain theft and the possibilities for recovery of the stolen domain names

Privacy Impact Assessment
Exceptions In Injected Code

Low fidelity prototyping: The cheapest corrections in design stage ever!

Owasp ZAP

Keeping Your Social Media Accounts Safe

Analysis of Malware Samples with the Immunity Debugger API

Eight Handy Security Tools for a Novice

Web Vulnerabilities Explained
Introduction to Anonymizing Networks – Tor vs I2P

Investigating the crime scene part 2: Recovering files with autopsy

Getting Domain Information

Chapter 12 – Applications of Biometrics

Backtrack 5 R3 Walkthrough, Part 4

Environment for Malware Analysis
Analyzing malicious JavaScript

Password Auditing on Active Directory Databases

Executable Code Injection

Wordfence: Security Plugin for WordPress

Backtrack 5 R3 Walkthrough - Part 3

Wfuzz and WebSlayer
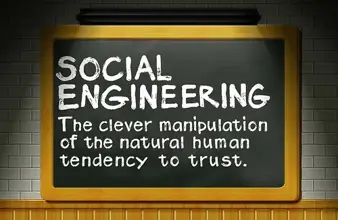
The easier form of hacking: Social engineering

The Internet Underground: Tor Hidden Services