Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
How to filter user input: An overview
IT Continuity Planning
Reverse-Engineering Arrays

How to Safely and Wisely use jQuery: Several Key Issues

Physical security: Managing the intruder
Virtualization security

Differences in Copyright Enforcement between the U.S. and China
Book Excerpt: Advanced Network Design, Chapter 4: Infrastructure

Wireshark
Google Hacking with GGGoogleScan

Network Scanning Using Nessus
Phishing: A Very Dangerous Cyber Threat

Tutorial on SQLi Labs

Demystifying dot NET reverse engineering - PART 3: Advanced Byte Patching
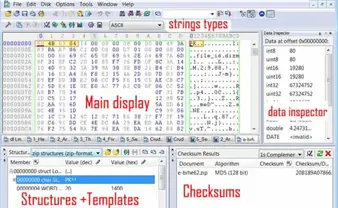
Hexed – Working effectively in the hex editor

Calling Conventions

Android and Java Native Interface

How do I go about hacking FTP? Part III

SQL Injection Through SQLMap Burp Plugin

How do I go about hacking file transfer protocol? Part II

Estimating Projects Part III

Using Sandboxes For Hostile Program Analysis

Websecurify Walkthrough, Web Application Penetration Testing Tool

How do I go about hacking file transfer protocol? Part I