Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Fixing CSRF vulnerability in PHP applications
Linux Kernel Development Process

Windows systems and artifacts in digital forensics, part I: registry

IOS Application Security Part 18 - Detecting custom signatures with Introspy

Social engineering: A hacking story
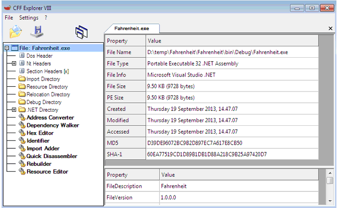
Patching .NET Binary Code with CFF Explorer

Conditional Complexity of Risk Models

Backup Media Encryption
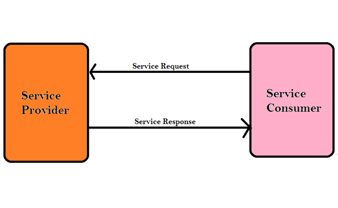
Web services penetration testing part 1

Hacking Satellites … Look Up to the Sky
Peeping the Social media

IOS Application Security Part 17 - Black-box assessment of IOS Applications using Introspy

Protect Data by Preventing Insecure Cryptographic Storage
System address map initialization in x86/x64 architecture part 1: PCI-based systems

Email encryption: Mailvelope

Online dictionary attack with Hydra
Penetration testing of web services with CGI support

OSINT (Open-Source Intelligence)
Phishing with Data URI
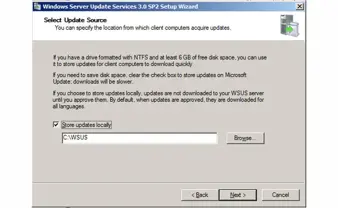
WSUS (Windows Server Update Services)
XKeyscore: NSA’s Surveillance Program
IOS Application Security Part 16 - Runtime Analysis of IOS Applications using iNalyzer

The Hunt for Memory Malware

Using Hashes in Computer Security