Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Beyond password length and complexity
HIDS—A Simplified Design Construct
Coding of Disassembler
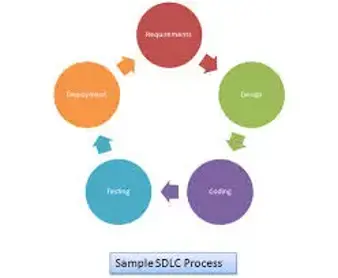
SCA, For a Secure SDLC

OSSEC
Cloud Forensics: An Overview

QEMU Windows Guest: Bridged Networking

QEMU Windows Guest: Networking

Forensic Investigation on Windows Machines

QEMU Windows Guest: Installing the Operating System

Security Predictions for 2014

Adobe CQ Pentesting Guide – Part 1
Securing Your Java Code 2

Vulnerability Scanning with Metasploit: Part II

The Mechanics of Metasploit

Business Continuity & Disaster Recovery

Steganography and Steganalysis: Common Image Formats and LSB Part 2

IOS Application Security Part 26 - Patching IOS Applications using IDA Pro and Hex Fiend

Unordinary Predictions for Information Security in 2014
Steganography and Steganalysis: Common Image Formats and LSB
Legality of DDoS: Criminal Deed vs. Act of Civil Disobedience
Firewall Unleashed

Android Application Penetration Testing: Setting up, Certificate Installation and GoatDroid Installation

Vulnerability Scanning with Metasploit Part I