Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
Security Awareness Course Design Best Practices
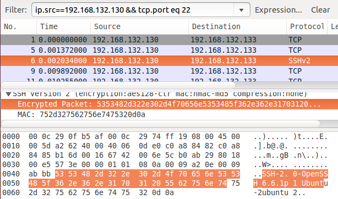
Snort Covert Channels
Security best practices for git users
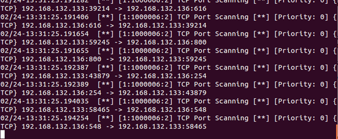
Snort network recon techniques
Social Networking Forensics with Bulk_Extractor

Using Mobile Devices for Hacking

Security Vulnerabilities of Internet-Connected Homes

Cyber Criminal Ecosystems in the Deep Web
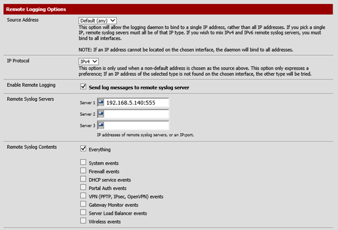
VoIP network recon: Footprinting, scanning, and enumeration
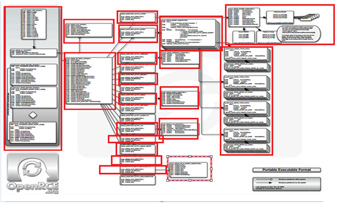
Complete Tour of PE and ELF: Directories
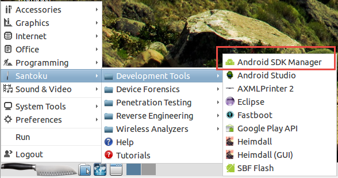
Android forensic logical acquisition
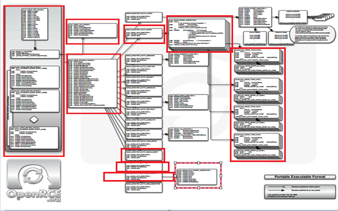
Complete Tour of PE and ELF: Data Structures
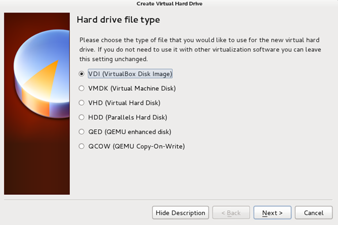
Configuring a Test Lab for Data Analysis
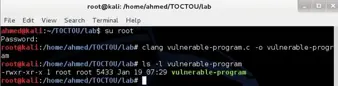
Race condition (TOCTOU) vulnerability lab
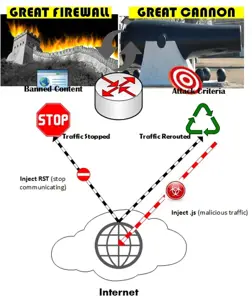
DDoS Attacks: Targets and ‘Smoke & Mirrors’ Mode

Top 7 Android Ransomware Threats

Developments in Machine Learning vs. Traditional SIEM Solutions

The Ferizi Case: The First Man Charged with Cyber Terrorism
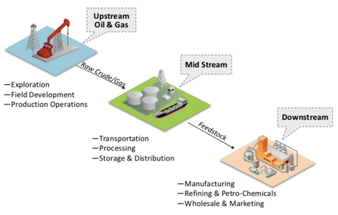
Oil and Gas Cyber Security 101
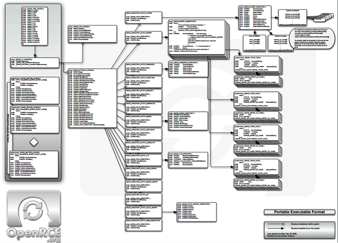
Complete Tour of PE and ELF: An Introduction

Is your Security Awareness Program Culturally Sensitive? (And does it matter?)
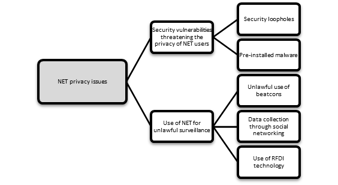
Legal issues of new and emerging technologies

Categorizing the Types of GNU/Linux users
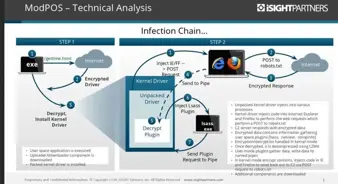
PoS Malware: All You Need to Know