Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
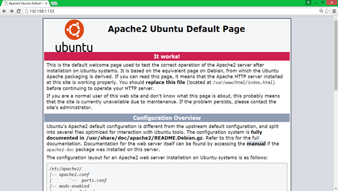
Public Key Infrastructure: Concepts & Lab Setup

Phishing Definition and History

Information Security Vulnerabilities of Trains
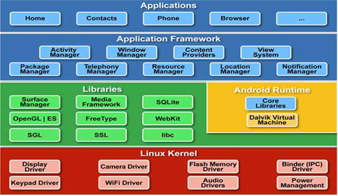
Android forensics labs
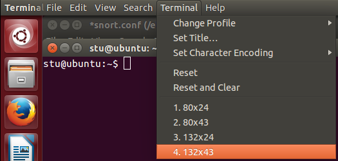
Snort Lab: Rule Performance Analysis
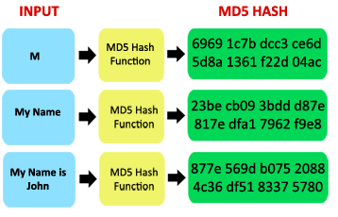
Cryptographic algorithms lab

Encryption Everywhere?
Panama Papers - How Hackers Breached the Mossack Fonseca Firm
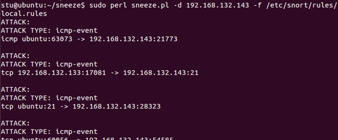
Snort Lab: Blinding IDS

CISA 2016 - What's New

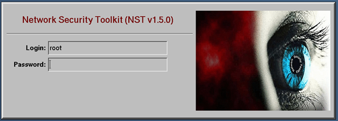
Implementation of a Virtual IDS Device in Passive Mode

How to write Phishing templates that work
Lessons from Writing Multiple-Choice Test InfoSec Questions
Snort Lab: Custom SCADA Protocol IDS Signatures
Forensic investigation with Redline
Important Code Constructs in Assembly Language: Advanced
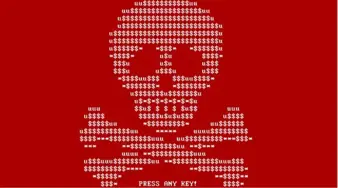
Ransomware in the Wild: It’s an Emergency
Snort lab: Payload detection rules (PCRE)
Important Code Constructs in Assembly Language: Basics
Snort Session Sniping with FlexResp
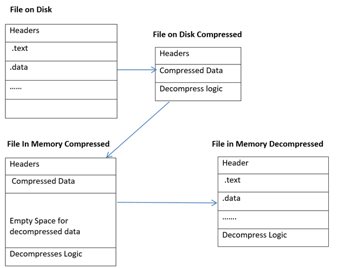
Complete Tour of PE and ELF: Section Headers

SAP Security – Think Different
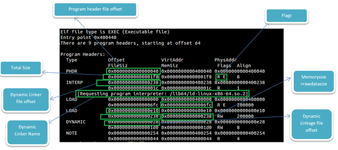
Complete Tour of PE and ELF: Structure
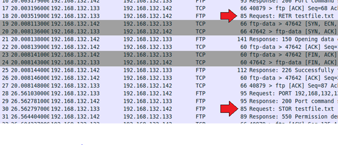
Snort Tracking Exploit Progress with Flowbits