Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
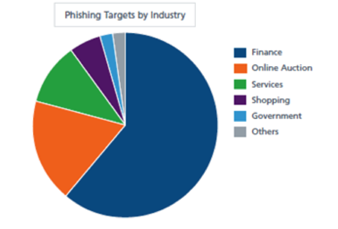
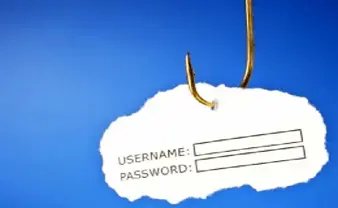
Phishing Attacks by Demographic
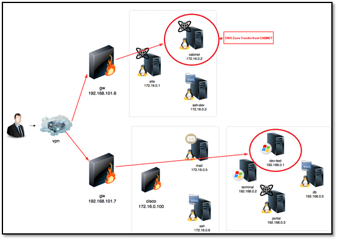
Test Lab V8: Recon and Dev-test
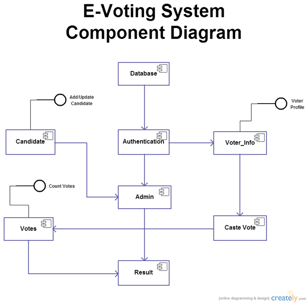
The Call for Online Voting: Are We Ready?
Non Technical Countermeasures
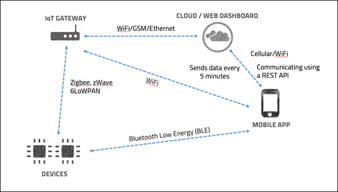
Getting Started with IoT Security - Mapping the attack surface
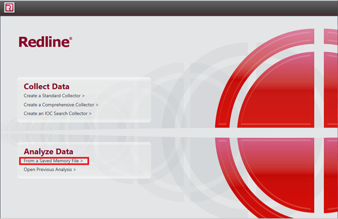
Memory analysis using redline
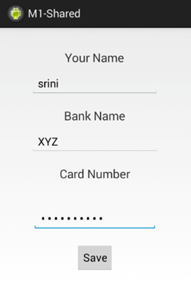
Android hacking: Dumping and analyzing application’s memory
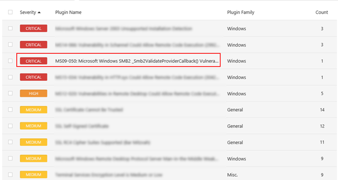
Black Box network penetration testing walkthrough

Gamification of Security Awareness Campaigns
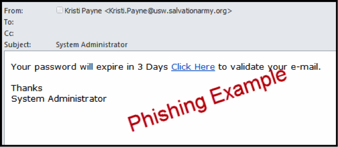
Phishing on Social Networks - Gathering information
Phishing Attacks on the Retail Industry
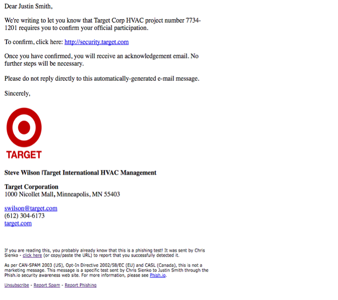
Penetration Testing and Cloud Platforms.
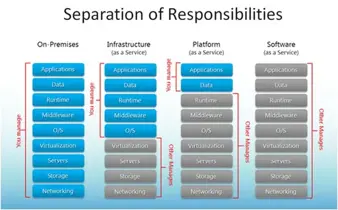
The art of searching for open source intelligence

A Hacker’s Tips for Running a Security Company

Mobile device penetration testing

ISIS Cyber Capabilities

Penetration testing of a citrix server

Phishing Simulation - How Do You Calculate Effectiveness and ROI? (Part 1 of 2)
Snort Lab: Activate / Dynamic Rules
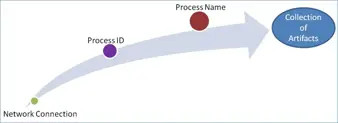
Memory Forensics
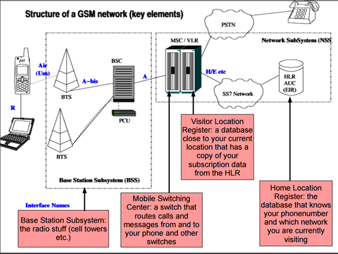
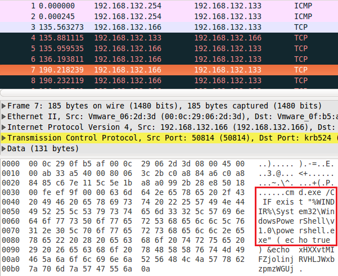
SS7 protocol: How hackers might find you
5 Reasons for Segmenting Your Phishing Simulation Campaigns
Mastering Mobile Forensics
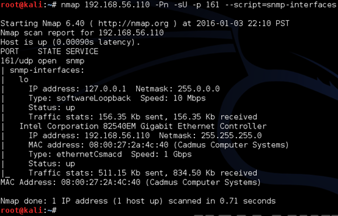
SNMP pentesting