Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
Moria: 1 - Walkthrough

The Dangers of the Windows Mobile Phone

A4 Black Friday: Massive Ransomware Attack Leveraging on Wannacry Hit Systems Worldwide

Kioptrix: Level 1 - Walkthrough

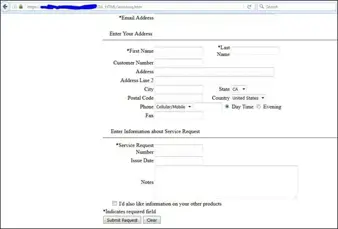
Dropbox Phishing Attacks- Templates and Examples

What is the HCISPP? Healthcare Information Security & Privacy Practitioner
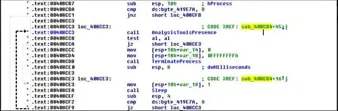
Malware Anti-Analysis and Bypassing its Techniques
SickOS 1.2: Walkthrough
Billu: B0x - Walkthrough

Security Assessment of CCTV
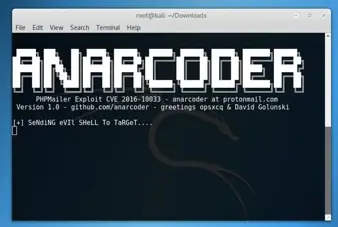
DonkeyDocker:1 CTF - Walkthrough

The Security Weaknesses of the iOS: The Aisi Helper, Sandjacking, and Image Threats
Misconfigured WAFs: Bypassing Broken Access Controls Protection

Advanced Techniques Attackers Use to Crack Passwords
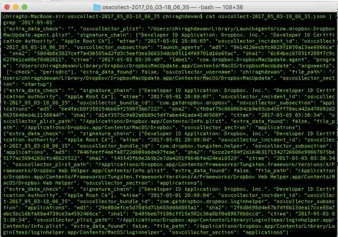
OSXCollector: Walkthrough

Steps to Stronger Passwords

Malware Anti-Analysis Techniques and Ways to Bypass Them

Error Message Phishing Attacks- Templates, Examples & Prevention Strategy

Artificial Intelligence and Its Impact on Cyber Security
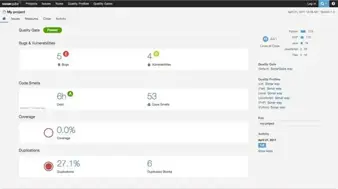
SonarQube: A Hidden Gem
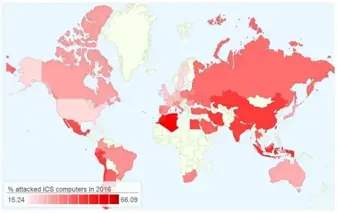
Cyber risks for Industrial environments continue to increase

Top Ten Phishing Scams

Shellcode Analysis- Basics
The Security Weaknesses of Smartphones