Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
SAP SECURITY FOR CISO: SAP Attacks and Incidents
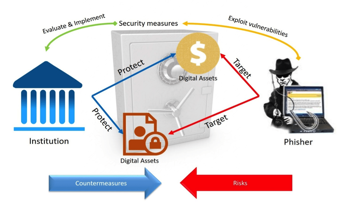
Anti-Phishing: Threat Modeling and Impact Analysis

“Robin Hood” Ransomware and Psychological Manipulation Techniques

Web application pentest guide Part-II

Anti-Phishing: Browser Security Features

Anti-Phishing: Measuring Phishing Awareness Training Effectiveness

Anti-Phishing: The Importance of Phishing Awareness Training

Introduction to Anti-Phishing
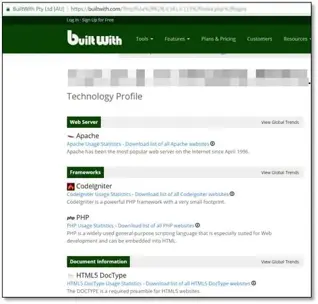
Web Application Pentest Guide Part-I

Ew! Skuzzy CTF Walkthrough
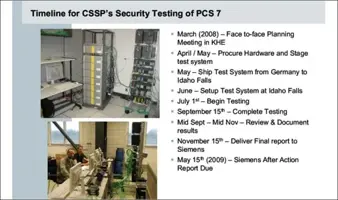
Which Malware are Specifically Designed to Target ISC Systems?
Big Data Discrimination
Troll 2 exploitation walkthrough

NAC-hacking - Bypassing network access control
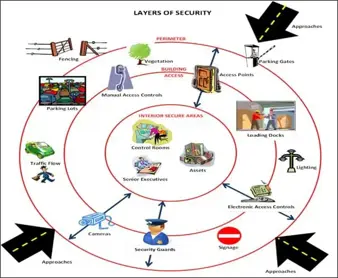
How Much Physical Security is Enough?

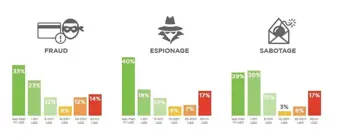
Security Awareness Implications of the 2017 Verizon Data Breach Report
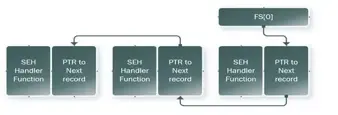
More Bypassing of Malware Anti-Analysis Techniques

Learning Pentesting with Metasploitable3 – Part 2
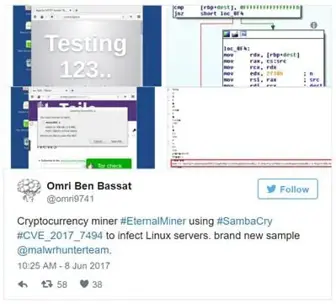
SambaCry: Hundreds of thousands of Linux systems exposed to a campaign that delivers cryptocurrency miner
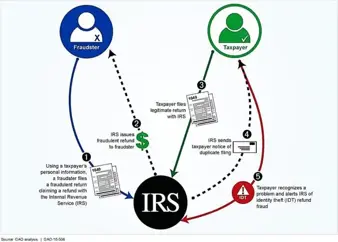
How to Protect Your Right to Personal Identity in the Digital Era
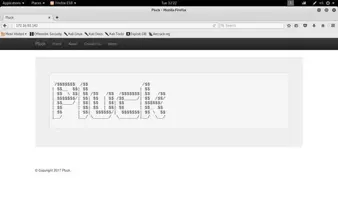
Pluck: 1 CTF Walkthrough

Top 7 Tips to Secure Your Passwords
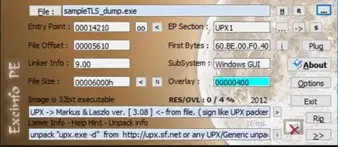
Malware Anti-Analysis Techniques-TLS and Process Hallowing

The Major Security Issues Surrounding Virtual Personal Assistants