Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

The concept of mobile phone

Feature Phone Forensics

Petya Ransomware Initial Analysis

SecOS: 1 CTF Walkthrough

The Ins and Outs of Email Security Awareness

Ways to Stay Secure When using File Sharing

Reverse Engineering – LAB 3

Practical android phone forensics

AlphaBay Market: What is the Impact of the Cyber-criminal Underground?

Vault 7 Data Leak: Analyzing the CIA files

Learning Pentesting with Metasploitable3: Exploiting WebDAV
More Security Issues Surrounding Virtual Personal Assistants
Learning Pentesting with Metasploitable3: Exploiting WordPress
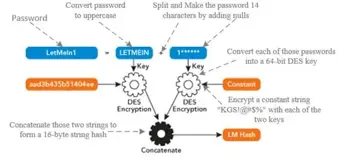
Exploiting Windows Authentication Protocols: Introduction

Security Awareness for Customer Service Representatives

Security Awareness for End Users

Phishing Checklist for Browsing Emails
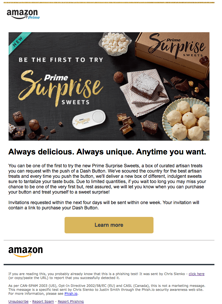
Amazon Phishing Template: Example and Preventing Attack

Mobile Systems Vulnerabilities

Trend Micro OSINT Challenge
Learning Pentesting with Metasploitable3: (Exploiting WebDAV)
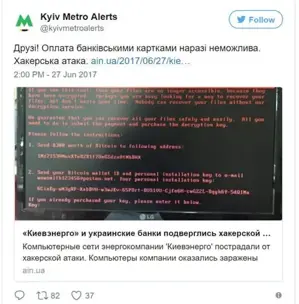
Massive Petya Attack: Cybercrime or Information Warfare?

/dev/random: Pipe CTF Walkthrough
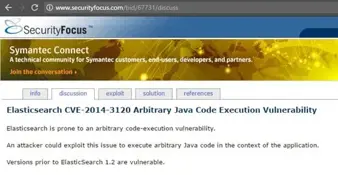
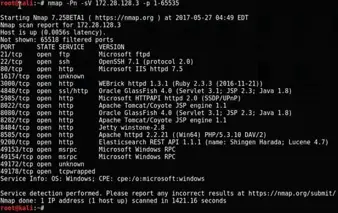
Learning Pentesting with Metasploitable3: Exploiting Elasticsearch