Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

The security awareness hazards of removable media
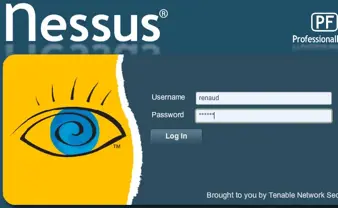
A guide to installing and using the Nessus vulnerability scanner

OWASP Top 10 #5: Security Misconfiguration

OWASP Top 10 #4: Broken Access Control

PHP Lab: Review the code and spot the vulnerability

OWASP Top 10 #3: Cross-Site Scripting (XSS)

OWASP Top 10 #2 - Broken Authentication Session Management

PHP Lab: Analyze the code and spot the vulnerability

OWASP 2017 top 10 vs. 2013 top 10

HBO Hacked, Game of Thrones script leaked on the Internet

PHP lab: PHP double submit problem.

PHP lab: File upload vulnerabilities:

PHP lab: File inclusion attacks

The Importance of C-Level Security Awareness Training

WannaCry, The Aftermath: How WannaCry Could Have Been WannaSmile

PHP Lab: Exploiting SQL Injection

Does History Need to Repeat Itself? Lessons Learned From WannaCry

How Security Awareness Training Can Protect the Military
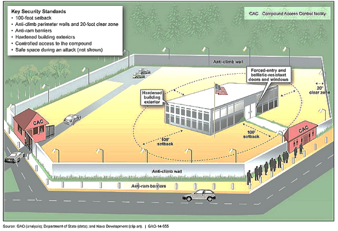
Tips for Managing Physical Security

PHP Lab: Prevent exposure of configuration/backup files from web root.

Average Data Recovery (CDRP) Salary in 2018

Reverse engineering a JavaScript obfuscated dropper

Top 20 Security Awareness Tips & Tricks

The Case for Annual Security Awareness Training