Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

How to land your first Penetration testing job

Automated Tools vs a Manual Approach
Open source threat intelligence tools & techniques

How to configure & use Suricata for threat detection

Computer Forensics: Forensic Issues with Virtual Systems

Security Assessment of a Digital Signage Solution

Android root detection bypass by reverse engineering APK
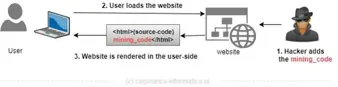
New Era of Crypto-jacking

The Ultimate Guide to CCSP Certification

15 best free packet crafting tools

From local file inclusion to code execution

Global Cost of Cybercrime on the Rise

Top 6 iPhone hacking tools for mobile penetration testers

Top 5 android hacking tools for penetration testers

10 Ways to Protect Your Identity and Prevent Identity Theft

Computer Forensics: Online Gaming and VR Forensics

Computer Forensics: ICS/SCADA Forensics

Computer Forensics: Big Data Forensics

Computer Forensics: Introduction to Social Network Forensics

Computer Forensics: Introduction to Cloud Forensics

Computer Forensics: Hybrid and Emerging Technologies

The Best & Worst Practices of Incident Response
Breach Notification Requirements for Healthcare Providers

9 Tips for Improving Your Incident Response Strategy