Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

A guide to preventing common security misconfigurations

Computer Forensic Report Writing and Presentation

10 Steps to Detect Lateral Movement in a Data Breach

Penetration Testing Methodology for Mobile Applications: 5 Key Steps

5 New Threats Every Organization Should be Prepared for in 2018
How to Complete a Vulnerability Assessment with Nessus

Expert Tips on Incident Response Planning & Communication

How to Use AlientVault SIEM for Threat Detection & Incident Response

QuadRooter Attack Overview: Vulnerabilities, Methods & Mitigations
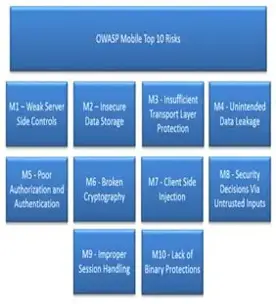
Comparing Mobile & Web Application Penetration Testing
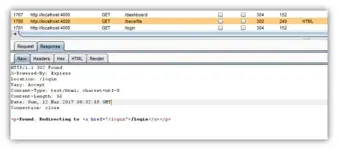
An introduction to penetration testing Node.js applications

Basic Principles of Ensuring iOS Apps Security
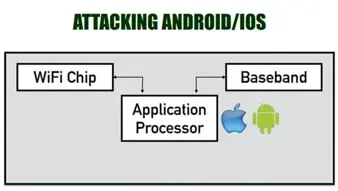
Broadpwn Wi-Fi Vulnerability: How to Detect & Mitigate

Top 10 Things to Look for or Avoid When Choosing a Pen-Testing Vendor
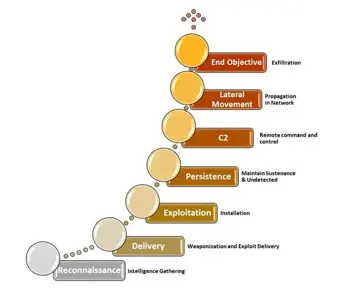
Advance Persistent Threat – Lateral Movement Detection in Windows Infrastructure – Part I
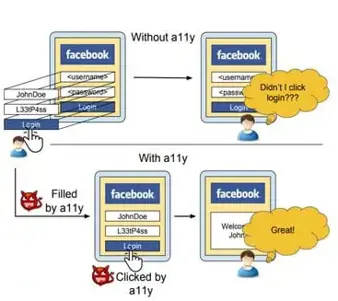
Understanding the Cloak & Dagger Attack: Overview & Tutorial

YARA: Simple and effective way of dissecting malware

ICMP attacks
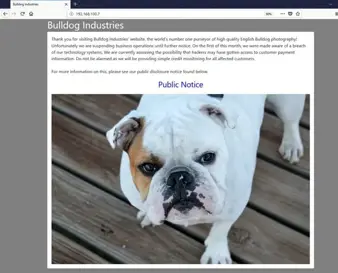
Bulldog: 1 CTF Walkthrough

Top 6 mobile application penetration testing tools

Memcrashed: The Dangerous Trend Behind the Biggest DDoS Attack Ever

Top 10 Reasons Why Pentesting is Important to Help Meet Compliance
Threat Hunting – Command and Control Center - OFFICE WORK
Top 5 Free Intrusion Detection Tools for Enterprise Network