Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
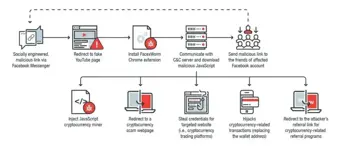
Crooks Exploit Facebook to Spread Crypto-miner Malware

The basics of IDA pro

Layer Seven DDoS Attacks
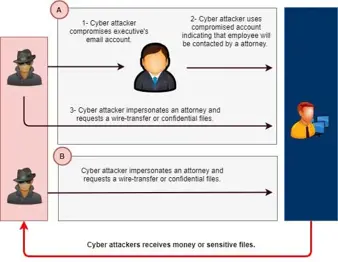
BEC Attacks: How Attorney Impersonation Works

5 reasons why you should report — Not reply to — Suspicious emails

BEC Attacks: How Fake Invoice Schemes Work
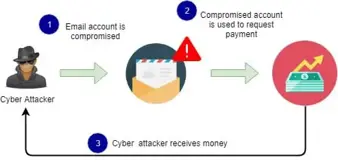
BEC Attacks: How Email Account Compromise Works

How to Recover from A Business Email Compromise (BEC) Attack
The importance of physical security in the workplace

Top Five SecurityIQ Phishing Templates: April Edition

Android penetration tools walkthrough series: Frida
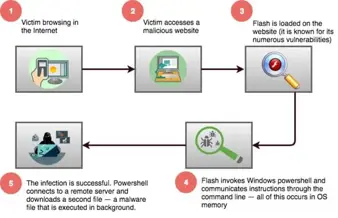
The Art of Fileless Malware

Threat Hunting – Chthonic Banking Trojan

What is the DoD CSSP (cyber security service provider)?
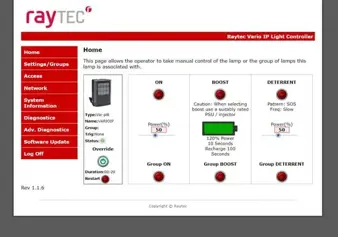
Shodan and IoT: The Problem is here!
How Criminals Can Exploit AI
How to Prevent BEC With Email Security Features
4 Ways to Integrate BEC Prevention Strategies into Your Organization

Cooperation between Humans and Artificial Intelligence in the Name of Security

CGEIT Domain 2: Strategic Management [DECOMMISSIONED ARTICLE]
Android Penetration Tools Walkthrough Series: Androguard

Null byte injection in PHP

Log analysis for web attacks: A beginner's guide

Configuration of Anti-Virus and Anti-Malware Software within an ICS Environment