Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
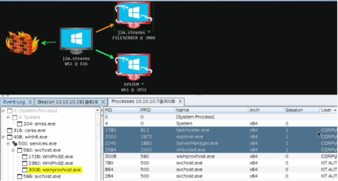
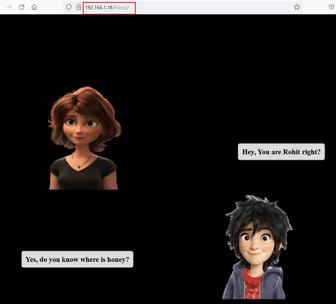
FINDING MY FRIEND: 1 VulnHub CTF Walkthrough - Part 1

Intrusion detection software best practices

What is intrusion detection?
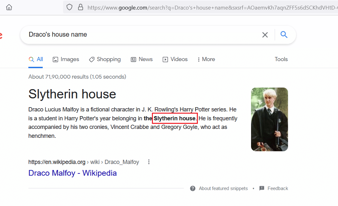
HOGWARTS: DOBBY VulnHub CTF Walkthrough

Looking to the future: A CISOs biggest challenges

CompTIA PenTest+ certification exam: Overview of domains

Log4j vulnerability explained: Zero-day attacks and how to contain them

The 7 steps of ethical hacking
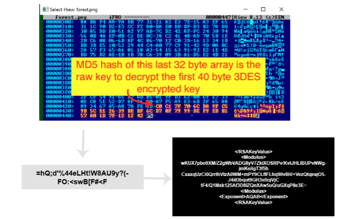
Modus operandi of BlackByte ransomware

Cybersecurity Weekly: 2022 email security trends, vulnerabilities in WordPress plugin and resources from CISA

Reducing cybersecurity risks with strong awareness reporting

Will immersive technology evolve or solve cybercrime?

Passwords and people: Your secret weapons against cybercriminals

Vendor-specific versus vendor-neutral: Best cybersecurity certifications

PenTest+ certification job titles and career outlook
Emotet malware returns

What is penetration testing, anyway?
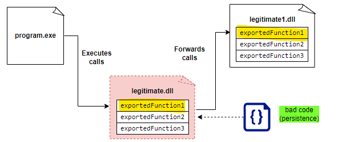
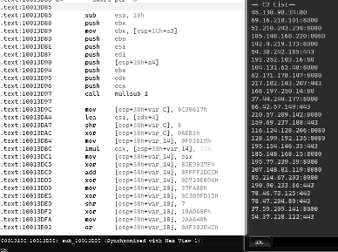
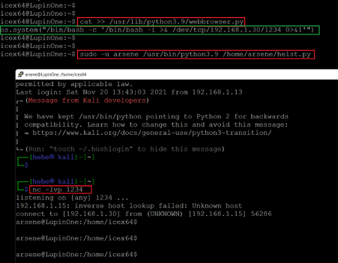
Red Teaming: Persistence Techniques

Cybersecurity Weekly: Framing security with leadership, ransomware advisories continue and biological models for cybersecurity predictions.
EMPIRE: LUPINONE VulnHub CTF Walkthrough, Part 2

Collaboration is key: IBM and Booz Allen Hamilton weigh in on attracting and retaining cyber talent

Finding the right MSSP for securing your business and training employees

Laravel authorization best practices and tips