Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
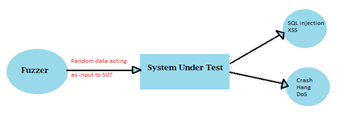
Fuzzing: Mutation vs. generation

LOIC (low orbit ion cannon) - DOS attacking tool

Web Analysis, Vulnerability Assessment and Exploitation using Backtrack5

Secure random number generation in JAVA

Enterprise Security: A practitioner's guide - Chapter 1

VLAN hacking

UEFI and the TPM: Building a foundation for platform trust

Goodbye DIACAP, Hello DIARMF

A history of anonymous

SQL Injection: The Equal Opportunity Vulnerability

Android malware analysis

HTTP response splitting attack

Understanding the Public Key Infrastructure behind SSL secured websites

Attacking web services Pt 2 - SOAP

Attacking web services Pt 1 - SOAP
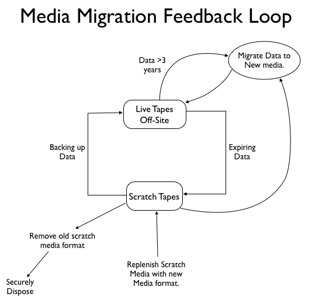
Are your backup systems secure?

Cracking WPA2 Tutorial

OWASP Top 10 Deeper Dive - A8: Failure to Restrict URL Access

IT auditing and controls - IT governance and controls

Web application testing with Arachni

Creepy, the geolocation information aggregator

The Case of the Great Router Robbery

IT auditing and controls - An introduction
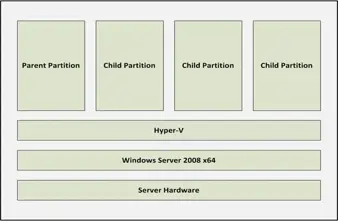
Microsoft Virtual Server Security: 10 Tips and Settings