Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Cybersecurity Weekly: Preparing for supply-chain attacks, new approaches to security awareness and a ransomware warning from the FBI

Cyber talent diversity: It's time to redefine the face of security

Want to lead a global privacy program? 6 things to know about CIPM

Cybersecurity and Windows 11: What you need to know

Data privacy careers: 6 key insights about this life-changing path

CompTIA PenTest+ domain 4: Reporting and communication
Log4j - the remote code execution vulnerability that stopped the world

3 major flaws of the black-box approach to security testing

Python scripting: A tool you need to learn and use for cybersecurity

Red Teaming: Top tools and gadgets for physical assessments

CompTIA PenTest+ domain 3: Attacks and exploits

Cybersecurity Weekly: The return of a dangerous botnet, malware in the GooglePlay Store and more

The NIST NICE Framework: How to improve cybersecurity role clarity and recruiting

Using Zeek for network analysis and detections

Suricata: What is it and how can we use it
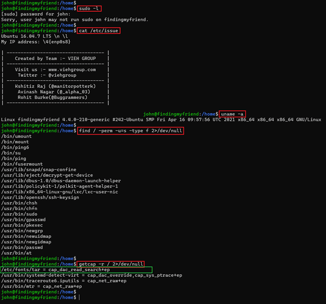
FINDING MY FRIEND 1 VulnHub CTF Walkthrough - Part 2

CompTIA PenTest+ domain 2: Information gathering and vulnerability scanning

How to choose and harden your VPN: Best practices from NSA & CISA

Can bug bounty programs replace dedicated security testing?
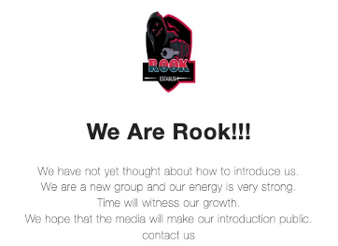
Rook ransomware analysis
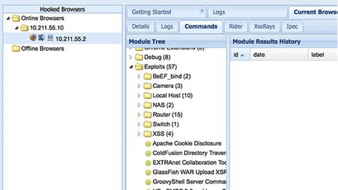
Red teaming: Initial access and foothold

CompTIA PenTest+ domain 1: Planning and scoping

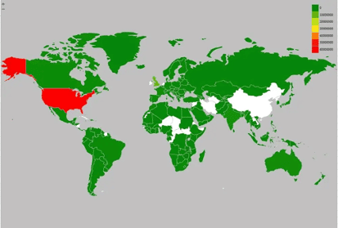
Intelligence brief: Russian invasion of Ukraine and its cybersecurity impact

Skills and experience needed to support a CSIRT, SOC or SIEM team