Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Estimating Projects, Part II

Estimating Projects, Part I

Filter evasion: Part 2

Filter Evasion: Part 1

Demystifying Dot NET reverse engineering, part 1: Big introduction
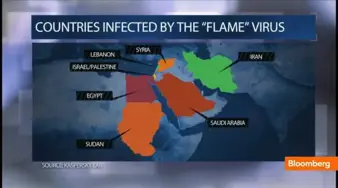
Flame: The Never Ending Story

X86 Assembly Language, Part 3.1

Apache JMeter Part 4: Testing the Throughput and Performance of InfoSec Institute

x86 Assembly Language Applicable To Reverse Engineering: The Basics – Part 1
Software Piracy - An Attempt to Assess the Problem

Raising a Rogue Access Point

The Rise of Cyber Weapons and Relative Impact on Cyberspace
Three Ways to Defeat a ReverseMe

Fuzzing Vulnserver with Sulley: Part 3

Fuzzing Vulnserver: Discovering Vulnerable Commands: Part 1

Getting Your Hands Dirty in x86 Assembly Code

Linux TPM encryption: Initializing and using the TPM
Packet Filtering

Security Categories

Linux TPM encryption: Enabling TPM in BIOS and Kernel

Good Programming Techniques - S.O.L.I.D. and Three-layer Architecture
Manual packet analysis

How to Use Iptables

Penetration Testing with the Joomla Security Scanner