Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
Anti-memory dumping techniques

Mobile working – prepare for the worst, deal with the fallout

Web Services

Logging Keystrokes with MSDOS: Part 1
The IA-32 Real Mode and Interrupts

Hacking java applications using JavaSnoop
Exception Handling
MSDOS and the Interrupt Vector Table (IVT)

Diving in the deep web
Building Security in Requirements

Legal Aspects of Online Gambling

Phishing Techniques: Similarities, Differences and Trends - Part II: Targeted Phishing
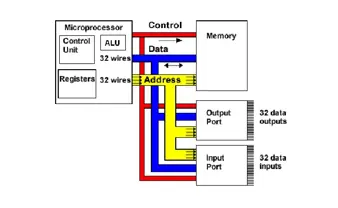
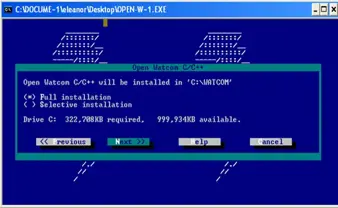
Memory Models

Paraben’s iRecovery Stick Review

ADO.NET architecture

Anti-forensics - Part 1

Automation Unit Testing with NUnit

Mobile Phone Spying Software: Legality, Symptoms, and Removal

Building Custom Controls in C# - Part 2

Building Custom Controls in C# - Part 1

Debugging with Visual Studio 2010

PHP: Build Your Own Mini Port Scanner

Hacking E-banking
Exception management