Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

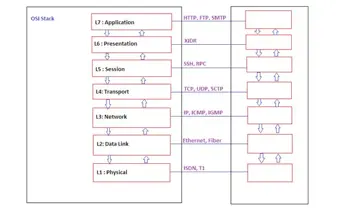
IOS Application Security Part 11 - Analyzing Network Traffic over HTTP/HTTPS

Rootkits On Your Smartphone

Confessions of an Identity Thief – Part 2

IOS Application Security Part 10 - IOS Filesystem and Forensics

.NET Reverse Engineering –Part 2

Facebook Technologies
How Edward Snowden protected information … and his life

The Mobile Device Management Saga: An SIEM (Security Information Event Management) perspective

Password Auditing Explained

Means and Methods of Web Tracking: Its effects on privacy and ways to avoid getting tracked

Fitting cyber attacks to jus ad bellum — Consequence-based approach, Part III

IOS Application Security Part 9 - Analyzing Security of IOS Applications using Snoop-it
Socket Programming
Password Cracking Evolution

.NET Assembly Programming

Fitting cyber attacks to jus ad bellum — Target-based approach

Confessions of an Identity Thief

Common Vulnerability Scoring System

.NET Reverse Engineering-1:CIL Programming

Fitting cyber attacks to jus ad bellum — Instrument-based approach
IOS Application Security Part 8 - Method Swizzling using Cycript
Programming with COM

The Palantir Technologies model, lights and shadows on a case of success

IOS Application Security Part 7 - Installing and Running Custom Applications on Device without a registered developer account