Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Gentoo Hardening Part 1: Introduction to Hardened Profile

What We Learned from APTs in the Current Year

Optimizing Managed Code Execution

Photo forensics: Detect photoshop manipulation with error level analysis

Symmetric and asymmetric encryption
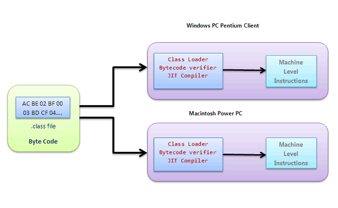
Demystifying Java Internals (An introduction)
Phishing Counter-Measures Unleashed
Brainpan

IOS Application Security Part 20 - Local Data Storage (NSUserDefaults, CoreData, Sqlite, Plist files)
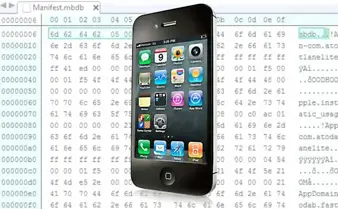
Will the iPhone 5S Be The Catalyst to Fingerprint Scanners on All Our Devices?

Port scanning using Scapy
Unsafe Programming

CSRF proof of concept with OWASP ZAP
BEAST vs. CRIME attack
Hardware attacks, backdoors and electronic component qualification

Identity Management and Access Control in a Single Sign-on Environment

File system manipulation

Portable Malware Lab for Beginners – Part 2
Managed C++/CLI Programming: Part 2

Estonia: To Blackout an Entire Country – Part 2

The BodgeIt store part two

The breach attack

Windows Phone Digital Forensics II

The BodgeIt store part one