Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources
Analyzing malicious PDFs
.NET reversing with Reflexil
Exploiting Linux Kernel Heap Corruptions (SLUB Allocator)

SIM card forensics: An introduction

IOS Application Security Part 23 - Defending against runtime analysis and manipulation

Human Factors in Information Security Management Systems

Risk associated with cookies
Privacy Implications of the Internet of Things
Tunnelling SSH Traffic
Reversing firmware part 1
Reverse Engineering with Reflector: Part 1

IOS Application Security Part 22 - Runtime Analysis and Manipulation using GDB

How Classified NSA Exploit tools RADON and DEWSWEEPER Work

Top Links of Tools Compilation for Pentesting, Forensics, Security, and Hacking
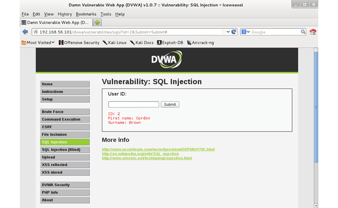
Fuzzing for SQL injection with Burp Suite intruder
IOS Application Security Part 21 - ARM and GDB Basics

Web Services Penetration Testing, Part 2: An Automated Approach With SoapUI Pro
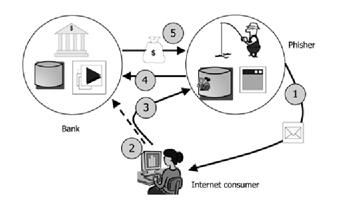
Modern Online Banking Cyber Crime
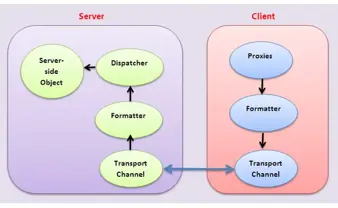
Remoting Technology

Gentoo Hardening: Part 3: Using Checksec

2013 - The Impact of Cybercrime

Reverse engineering with OllyDbg

Gentoo Hardening: Part 2: Introduction to PaX and Grsecurity
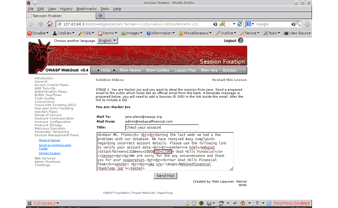
Understanding Session Fixation