Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Securing VoIP systems

Securing Shared Preferences with Third Party Libraries
Blackbox Assessments with Introspy

Bringing Down Security Risks With A BYOD Encryption Policy

Have New Backdoors Been Discovered in iOS? An Interview With iOS Developer and Digital Forensics Expert Jonathan Zdziarski
Xplico
Shellcode Detection and Emulation with Libemu

Crowdsensing: State of the Art and Privacy Aspects
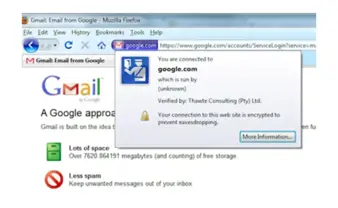
How cybercrime exploits digital certificates
Padding oracle attack
Pafish (Paranoid Fish)

Explaining cyberterrorism

Configuring the ModSecurity Firewall with OWASP Rules

File integrity monitoring (FIM) and PCI-DSS

Computer Forensics with P2 Commander
DragonFly, Cosmic Duke and Pitty Tiger: From State-Sponsored Espionage to Campaign of Independent APTs

Honey Encryption
Windows Cryptography API

Advanced sqlmap

Data loss prevention (DLP) strategy guide

Insecure local storage: Shared preferences
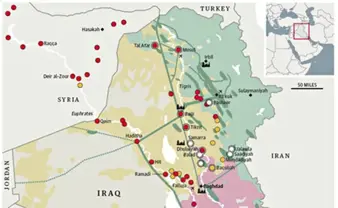
Islamic State of Iraq and Syria (ISIS) a Global Threat: Analysis of the Effects on Cyberspace of the Iraqi Situation

Root detection and evasion

Why Passwords Won’t Die