Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

How a DNS Sinkhole Can Protect Against Malware

Tracking Attackers with a Honeypot - Part 2 (Kippo)

Three Security Practices That IoT Will Disrupt

Data Backups with Bacula: Mobile Devices

Phishing WhatsApp Images via USB, From Python With Love

Preparing for a successful IAM integration project (Part 2 of 2)

Data Backups with Bacula: Notifications

Alleged Hack of iCloud Exposed Nude Photos of Celebrities Online
Hacking traffic light systems

Data Backups with Bacula: Backup Encryption

Data Backups with Bacula: Client Data Backup and Restoration

Data Backups with Bacula: Bacula Internals

Data Backups with Bacula: Creating the Storage Partition
iOS Application Security Part 35 - Auditing iOS applications with iDB

Windows registry analysis with RegRipper – A ‘hands-on’ case study

Exploiting Systemic Query Vulnerabilities: Why You Should Not Attempt to Re-invent PDO
PGP Alternatives for Email Encryption

Getting started with android forensics
Microsoft NAP (Network Access Protection)
Operation Emmental: Banking Hit by Even More Sophisticated Cyber Attacks

Windows registry forensics using ‘RegRipper’ command-line on Linux

Cyber Insurance
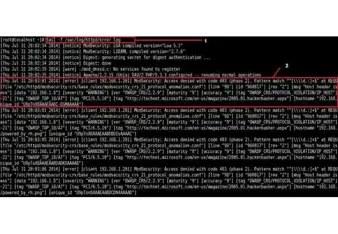
Analyzing the mod security logs
Cookies with Secure Flag: Undesired Behavior in Modern Browsers