Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

CompTIA A+ domain 2: Networking — What you need to know for the exam

CompTIA A+ domain 4: Virtualization and cloud computing — What you need to know for the exam

CompTIA A+ domain 5: Hardware & network troubleshooting — What you need to know for the exam

CompTIA’s A+ exam: 220-1102

CompTIA A+ domain 6: Operating systems — What you need to know for the exam

CompTIA A+ domain 7: Security — What you need to know for the exam

CompTIA A+ domain 8: Software troubleshooting — What you need to know for the exam


Top 30 A+ interview questions [2022 update]

9 online tools for malware analysis

Keeping your team fresh: How to prevent employee burnout
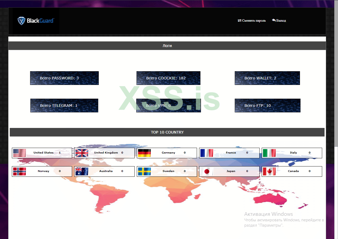
Blackguard malware analysis

Behind Conti: Leaks reveal inner workings of ransomware group
I failed my CREST Certified Infrastructure Tester exam: Here’s my story

Planning for post-quantum cryptography: Impact, challenges and next steps

What is Digital Risk Protection (DRP)?

ZLoader: What it is, how it works and how to prevent it | Malware spotlight [2022 update]

How foundations of U.S. law apply to information security

Deepfake phishing: Can you trust that call from the CEO?

CompTIA’s A+ exam: 220-1101
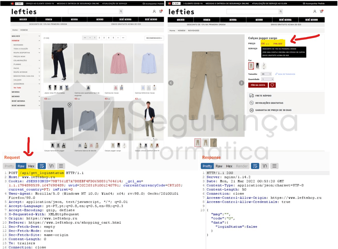
Fake shopping stores: A real and dangerous threat

WhisperGate: A destructive malware to destroy Ukraine computer systems

Security risks of cloud migration

How to become an ethical hacker: Tips from Offensive Security CEO Ning Wang