Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

Hackers Selling Healthcare Data in the Black Market
Securing Cookies Using HTTP Headers

Interview: Chris Camejo, Director of Assessment Services for NTT Com Security
NodeJS Security for Beginners

5 Reasons Your Business Needs a Data Recovery Partner
Cyber savvy? Take a Quick Security Awareness Quiz to Find Out

Maligno: An Open Source Pentesting Tool
Playing Hide-and-Seek with Metadata

Rootkits: Kernel Mode
Are You InfoSec Geek Enough? Take This Quiz and Let’s See What You Got!

35 Awesome InfoSec Influencers You Need to Follow

Rootkits: User Mode

Interview: Steve Lufkin, CEO of Vantix Diagnostics

15 Must Have Books for InfoSec Enthusiasts and IT Security Professionals

Lessons from Deficient Java Applet-based Authentication
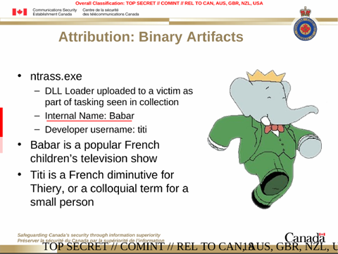
Animal Farm APT and the Shadow of French Intelligence

HTTP/2: Enforcing Strong Encryption as the De Facto Standard
Insecure Data storage with NoSQL Databases

How to Deal with Reverse Domain Name Hijacking

MOOSE Malware: Analysis

Social Engineering - A Case Study

The Top Five Cyber Security Vulnerabilities

Win32/Lethic Botnet Analysis

Office 365 Compliance Matrix