Security Awareness & Training Resource Center
Featured content

Deconstructing Human-Element Breaches | Infosec HRM
Human risk management isn’t just rebranded SA&T — it’s a profound change of mindset, strategy, process and technology that approaches human-related breaches in a new way.
![Inside an Infosec Boot Camp: All your questions, answered! [replay]](/globalassets/is-wb-24-05-inside-an-infosec-boot-camp_thumbnail2.webp?width=338&height=304&rmode=Max&bgcolor=transparent)
Inside an Infosec Boot Camp: All your questions, answered!
You need to get certified, but is an Infosec Boot Camp the right choice for you — or your team? Find out in this live Q&A with two Infosec instructors.

Emerging trend checklist: Which certifications cover which new skills?
Boost your team's cybersecurity skills with the right certifications. Discover the most in-demand skills and the certifications that cover them in our free guide.

Security Awareness Outcomes with Infosec IQ
See security awareness and training outcomes from more than five million Infosec IQ learners.
Our resources

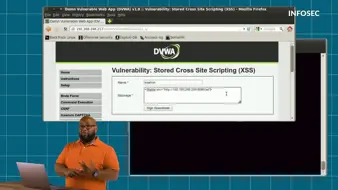
How cross-site scripting attacks work | Cyber Work Applied
Inside Equifax's massive breach | Cyber Work Applied

Cryptography basics: How does encryption work? | Cyber Work Applied
How to carry out a watering hole attack | Cyber Work Applied
Using password cracking tools: How to crack a password | Cyber Work Applied

How to use the MITRE ATT&CK matrix | Cyber Work Applied
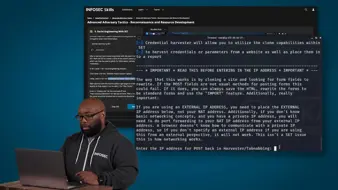
Reconnaissance and resource development with MITRE ATT&CK | Cyber Work Applied

Hashing basics: How does hashing work | Cyber Work Applied
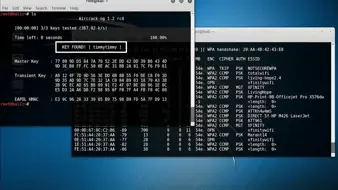
Wi-Fi password hack: How to hack into WPA Wi-Fi and WPA2 | Cyber Work Applied
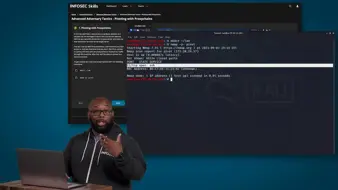
Pivoting with Proxychains with MITRE ATT&CK | Cyber Work Applied
Inside Capital One’s game-changing breach | Cyber Work Applied
Executing the Sandworm APT with MITRE ATT&CK | Cyber Work Applied

Inside a DDoS attack against a bank | Cyber Work Applied
Privilege escalation via cross-site scripting with MITRE ATT&CK | Cyber Work Applied
How Zoom is being exploited for phishing attacks | Cyber Work Applied
Persistence: Maintaining a foothold with MITRE ATT&CK techniques | Cyber Work Applied

Extortion: How attackers double down on threats | Cyber Work Applied

Understanding identification, authorization and authentication | Cyber Work Applied
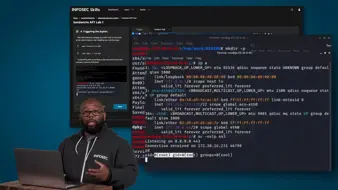
Advanced adversary tactics and defense evasion with MITRE ATT&CK | Cyber Work Applied

Getting started in cybersecurity | Cyber Work Applied

Secure cloud computing: What you need to know | Cyber Work Applied
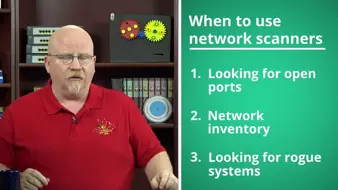
How to use Nmap and other network scanners | Cyber Work Applied

Password security: Using Active Directory password policy | Cyber Work Applied

Using AI to level up phishing attacks | Cyber Work Applied